Security Information & Event Management Software from SolarWinds
What SIEM does is merge Security Information Management (SIM) with Security Event Management (SEM). SolarWinds dashboard provides a graphical representation of the log data generated by your network devices.
If you need to make sure that your IT department's security is compliant with a USA standard such as PIC-DSS, HIPAA, GLBA, NERC or CIP, then work smart; employ SolarWinds SIEM to automate the task of maintaining your network security's integrity, and thus prevent cyber-attacks and data theft.
SolarWinds' SIEM Software Suite
Each of these is a stand-alone component, select what you need to protect your IT infrastructure.
- Log & Event Manager (LEM)
- Firewall Security Manager (FSM)
- Serv-U Managed File Transfer Server (MFT) and FTP Server
SolarWinds Log & Event Manager (LEM)
Collecting all the server and network device logs is the first step in your SIEM strategy. SolarWinds Log & Event Manager will handle all these logs in real-time, and also provide secure archiving and detailed reporting.
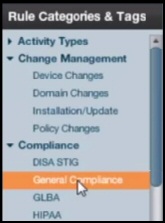
The clever part of LEM is log CORRELATION; the SolarWinds engineers have perfected rules to evaluate the captured data, and then automatically detect if there has been a security violation. The dashboard gives you dozens or rules or templates to choose from, and you can get expert support from the thriving Thwack forum.
The final part of LEM is configuring what to do in the event of a security breach; using a widget in the dashboard you can specify what to disable, which processes to kill, whether it's necessary to shut down a server, see below for a diagrammatic view of the SIEM process.
SIEM in Action
With SolarWinds graphical representation of the log data, you are limited only by your imagination when undertaking a forensic examination, or an analysis of historic data.
Drill down to see which user is generating most of the logs, also view data in real-time to investigate what's happening. Set a filter to home-in what is causing the data spike, configure email alerts to see if the pattern occurs again.
Video Explaining How to Create Rules for SIEM
by Rob Johnson, of SolarWinds
Here is a look at SolarWinds' LEM software in action. Rob will show you how to setup the LEM connectors, and then demonstrate how to select built-in templates to create rules that will analyze a network.
See much more on SolarWinds Log & Event Manager
Firewall Security Manager (FSM)
The key to successfully managing any firewall is spending time fine-tuning the rules that control what traffic can pass through this security gate. SolarWinds' firewall rule analyzer will guide you through optimizing your configuration by identifying weaknesses in any layer 3 network device.
The firewall manager will also relieve you of the admin needed for audit reports to comply with USA standards such as NIST, NSA or SANS.
I particularly like the 'Rule Cleanup and Optimization' facility; it's really good at indentifying obsolete rules and thus improving the firewall's performance.

One more useful feature is Change Impact Analysis. This enables you to evaluate 'What if' strategies when you are contemplating changing your firewall rules.
SolarWinds Serv-U Products (MFT and FTP)
The final piece in the Security Information & Event Management jigsaw is file transfer. Here are considerations for managing the security of your data files when at rest or when transported around your network.
- Security while data is in motion or at rest.
- Limit access to Directory Information, by role, individual and specific hours.
- File Storage: Limit access after upload, default file access policy and security logs
- Endpoint Management: Create, edit and remove trading partner profiles.
- Authentication through its support of multi-factor verification.
SolarWinds' Serv-U Gateway also provides a secure reverse proxy that prevents data from being stored at rest in a DMZ segment, it also prevents connections from being initiated from the DMZ into the internal network.

Computer and Network Performance
In addition to providing the Log & Event Manager, SolarWinds have an Orion suite of applications, most notably the Network Performance Monitor (NPM). The difference between these two apps is that LEM is concerned with monitoring the logs, then providing alerts and corrective action. Whereas NPM provides a dashboard with readings for factors such as CPU load (say 25%), capacity utilization (e.g. 67%) or network latency (350ms). It’s often only by comparing two tools that you get true understanding of what each can achieve, evaluate the Network Performance Monitor (NPM).
Summary: Review of SolarWinds SIEM
Employ a professional package such as SolarWinds Log & Event Manager that will effectively handle the event information generated by the logs that are already produced by your network devices. Monitor, identify, and then respond to security threats while reducing unnecessary false-positive alerts.
As a by-product of effect SIEM, you can achieve compliance with PIC-DSS, HIPAA, GLBA, NERC or CIP standards.
Free and 30-day Trial Virtual Machine Software
Here are my recommendations for additional handy utilities. Many of these downloads are free, while others are fully-functional, but time limited. SolarWinds are happy to provide you with a free specialist tool, which is ideal for testing, and then supply a more comprehensive suite for larger organizations. To let you into a secret, for small networks, the free tool is all you’ll ever need.
• Virtualization Manager • SolarWinds Application Monitor • Storage Response Time Manager
• VM Monitor • User Device Tracker • Free Network Bandwidth Monitor • Free SNMP Tool
• VM-to-Cloud • SolarWinds WMI Monitor • LanSurveyor • SolarWinds SIEM • Home