Introduction to Accounts Security in Windows Server 2003
There is a great deal that you can do to enforce account security, but before you get too carried away, ask yourself these two questions:
Who are our enemies? Internal meddlers, external hackers or both?
What is our security level? Low, Medium, or High. (High would be banks, MI5 or CIA)
My point is that too much security could alienate your work force, especially if the reasons for your measures are not properly explained. So integrate your security with your company culture and give horror stories to explain why account security is necessary.
Topics for Account Security
- Security concerns
- How do you stop these intruders?
- Where do you apply the security?
- Technology to the rescue – smartcards
‡
Security concerns
The fear is that non authorized people will misuse your network resources.
What are these people like? Malicious, opportunitistic or just curious.
What might they do? Steal data, read information or just alter settings.
How do they gain access? Guess passwords, sit down at unattended machines or just read post-it notes with passwords.
How do you stop these intruders?
Methods include:
- Account security, example Enforce strong passwords
- Physical security, example lock the server room.
- User education, explain the need to protect passwords
- Company policy, explain what constitutes misuse of the network
Develop a vision
Make your goal is to allow the good guys to work unhindered whilst keeping out the bad guys.
Involve someone who knows the users and understands how they work and what they think. Commit to developing and evolving your account security policy. It may be too draconian so slacken off, it may be breached so you need to tighten up in the light of experience.
- Make my system like fort Knox. – Overkill
- A secure workable system that people will understand and respect. – Yes
- Make everyone administrators. – No!
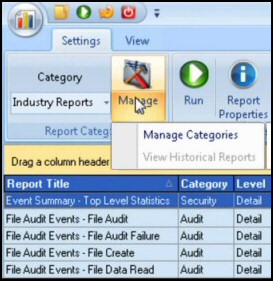
Guy Recommends: SolarWinds’ Log & Event Management Tool
LEM will alert you to problems such as when a key application on a particular server is unavailable. It can also detect when services have stopped, or if there is a network latency problem. Perhaps this log and event management tool’s most interesting ability is to take corrective action, for example by restarting services, or isolating the source of a maleware attack.
Yet perhaps the killer reason why people use LEM is for its compliance capability, with a little help from you, it will ensure that your organization complies with industry standards such as CISP or FERPA. LEM is a really smart application that can make correlations between data in different logs, then use its built-in logic to take corrective action, to restart services, or thwart potential security breaches – give LEM a whirl.
Download your FREE trial of SolarWinds Log & Event Management tool.
Where do you apply the security?
Through Group Policy, at the Domain level (not the OU or Site level).
The picture opposite shows what Windows Server 2003 offers. If you choose: Password must meet complexity requirements, it means, upper case, lower case, number non-alphanumeric (@ #).
Make users change their passwords every x days, and remember the last y passwords. Note use minimum password age or else they will just cycle through y passwords in their tea break, and come back to the original password!
What other settings can you apply through Group Policy? Check out the Account Lockout, this is where you can stop malicious people endlessly guessing someone else’s password. The downside with setting the values too low is that people may forget their own password and lock themselves out, thereby causing resentment and extra work for the help desk.
Technology to the rescue – smartcards
User authentication is a fundamental property of all computer systems. Passwords have always been the Achilles’ heel of computer security. Smart cards in some shape or form, have been ‘around the corner’ for about ten years.
I predict that within 5 years password logons will be obsolete. What will replace them? Smart cards, finger print logon, retina scanning some other technology. In fact if there were one clear market leader then the solution may be more obvious.
My advice is to consider what $25 will get you in the way of smart card keyboard attachments. The costs of doing away with passwords will pay back handsomely when you consider support calls and user frustration. Let us not forget the overall goal, a secure and friendly system.
Once you have the hardware, the software is easy, just check out the User Properties, Account tab.
Understanding the technology will help you secure your system. Guy’s rule of thumb is that the more security you have the more difficult it is to understand and the more work there is configuring it. Nevertheless you must secure your system and to do that you have to understand the components and procedures involved in Windows Server 2003.
Guy Recommends: Permissions Analyzer – Free Active Directory Tool
I like thePermissions Monitor because it enables me to see quickly WHO has permissions to do WHAT. When you launch this tool it analyzes a users effective NTFS permissions for a specific file or folder, takes into account network share access, then displays the results in a nifty desktop dashboard!
Think of all the frustration that this free utility saves when you are troubleshooting authorization problems for users access to a resource. Give this permissions monitor a try – it’s free!
Download Permissions Analyser – Free Active Directory Tool
If you like this page then please share it with your friends
Related topics
• Accounts • Auditing • IPSec • Kerberos Tickets • Windows RIS Server