
SIEM stands for Security Information and Event Management. This is a category of software that keeps track of events on a computer or network to guard against malicious intrusion. The term combines two system security methodologies. These are Security Event Management (SEM) and Security Information Management (SIM).
>>>Jump to the list of the best SIEM tools and software<<<
SEM systems raise alerts about suspicious activities on a computer or a network. A SEM tool monitors a series of interfaces and tracks events that occur on them, showing those events on the system console and also writing them to log files. A SIM system is mainly concerned with the contents of log files. As a rule of thumb, reporting on live events is the sphere of SEM and analysis of event records is the purpose of SIM.
Contents
There are a number of gray areas between SEM and SIM, which is why it is better to look at event messages in terms of SIEM, the unified security software category. One aspect of a responsibility that could be the responsibility of either SEM or SIM or both is the monitoring of log file integrity. Hackers know about the existence of event logs and so cover their tracks either manually or through a Trojan element by deleting or altering any records in the event logs that might have recorded the malicious activity. The alteration of log files is a security event, and so should be monitored by SEM. However, SIM is concerned with log file data, and so protecting that source information should be part of SIM. Whether log file integrity is part of SEM or SIM, it certainly is part of SIEM.
The importance of SIEM
No computer is completely immune to malicious intrusion or attack. The minute a file gets copied onto a computer, the risk of virus infection increases. Even a pristine computer bought by a programmer that will never have software installed on it from external sources is at risk if it has an operating system. Even a computer without an operating system could potentially get infected because all of the electronic components on the motherboard has embedded firmware in it.
The vast majority of the world’s population would find little use from a computer without an operating system or any software at all, and so we all run a security risk. Connecting a computer to the internet escalates the risks, and wifi capabilities mean that hackers can get at your computer through the walls even when the device is turned off.
The development of event logging means even if there is an intrusion on your computer or network, there will be a record of that activity. If you want to fix a problem, the first thing you need to find out is what caused it. That is what event logging provides.
Unfortunately, the designers and writers of programs can’t predict what methods intruders will use in order to interfere with a computer. There is no way of knowing well in advance, what new techniques will emerge someday. So, just to be on the safe side, software producers generate event log messages for just about every little bit of activity. This results in thousands of mundane and apparently innocuous messages written to log files.
SEM systems can filter out relatively unimportant event messages. However, SEM misses certain activities because a malicious activity can be broken down into a series of steps, which individually seem harmless but when viewed as a group highlight suspicious activities.
SIM systems look for patterns of activities that are recorded in log files. A computer program is much better at spotting data in thousands of records that the human eye ever could. The sheer volume of event log records means that it is impossible to read through them manually.
The advantage of the SIM approach is that a sequence of events that amount to malicious activities can be seen from the historical perspective. The disadvantage of SIM is that it can only see malicious activity once it has already occurred.
The combination of SEM and SIM into SIEM tries to use all available methods to shore up a system on the fly. If some activity slips by the SEM guard, the SIM processes will spot it – better late than never.
Why use SIEM?
You may think that you and your company are relatively unimportant and no genius hacker team in the depths of China or Russia is going to put its time and skills into breaking into the network of your party balloon factory. You’d be wrong.
If your company has a bank account, it can be useful as a front for a loans scam, a collection point for money extorted from other businesses, or a money laundering sluice for drug smugglers. If your company has an internet connection, it can be used to disguise the true origins of attacks on other companies, government agencies, or utilities. If a hacker gets into the network of your mundane business and erases event log entries that highlight his presence, you’re on the hook when the FBI traces the illegal activity as far as your network.
Every computer and internet connection has a value and unprotected, mundane businesses are great disguises.
So, everyone needs to take all possible steps to block intrusion. A category of intrusion called advanced persistent threat (APT) involves a hacker getting access to a computer or network and nesting. APTs can go undetected for years, leaving your company vulnerable to scams, data theft, and the liability for crimes committed against others launched from your internet address.
Although SIMs might appear to be operating after the damage has been done, they are particularly useful for blocking or, at least documenting APTs. If your event logs are protected and cannot be corrupted, hackers are more likely to leave your system alone. They don’t want to leave any record of their presence that could assist the Feds in tracing the source of an attack through your company and back to their real location.
SIEM activities
There are a number of distinct activity categories that every SIEM must include:
- Data collection and centralization: A typical SEM requires several information sources, collected at different points on the network. Their sources are disparate and include security software, such as firewalls, databases, and applications. These records need to be consolidated and adapted to a common format.
- Correlation: Links event messages together to create a composite record of a malicious attempt.
- Alerting: Notification to human controllers of possible malicious events. These should be noticeable messages either highlighted in dashboard screens or sent as email or SMS messages.
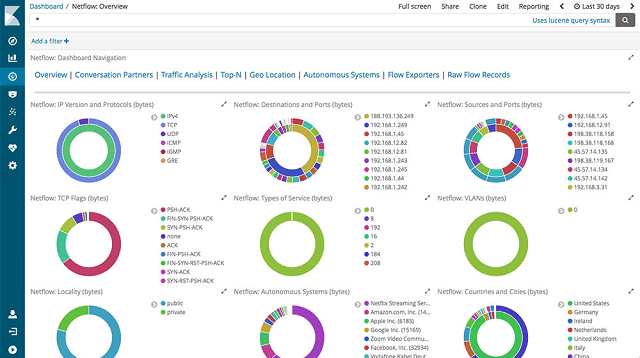
- Visualizations: SIEM systems need to be able to represent activity data in graphical format, such as charts, dials, and graphs. These devices speed up threat recognitions because they are easier to comprehend than sets of text records.
- Compliance: Threat detection and prevention is an activity that interests a range of stakeholders and may form part of a contractual obligation. The implementation of security standards acts as a shorthand for a set of data integrity and protection requirements and all of these steps need to be confirmed and logged in order to confirm compliance.
- Data Retention: Long-term data storage is necessary in order to prove system integrity at any later date. Historical data is needed both as evidenced for the operator’s defense and as source material from deeper intrusion detection and security research. Storage formats need to be indexed and organized in a logical manner in order to aid access.
- Forensic analysis: This refers both to human investigations supported by tools bundled into the SIEM system and machine learning techniques performed by the SIEM software.
A SIEM system should be able to adjust its strategies through references to historical attack patterns. Intrusion strategies change constantly and SIEMs need flexible detection routines that will adapt instead of becoming obsolete.
SIEM elements
Each SIEM product does not necessarily need to be comprehensive. It is perfectly legitimate for a tool to provide just one SIEM service and still be categorized as a SIEM service.
The most fundamental SIEM component, event messages, aren’t normally generated by SIEM software. Instead, they are created by messaging standards that are integrated into all of the other software operating on your network. The collection, manipulation, and storage of that data lie at the core of SIEM. However, they are not the only responsibilities of SIEM.
Log message collection
Your SIEM has a range of data sources available to it. Syslog is an industry standard event messaging system and many of the software and equipment on your network will be generating and circulating Syslog messages automatically right now, whether or not you are aware of their existence. The Windows Event Log system is another automatic source of event data. The Simple Network Management Protocol (SNMP) is built into every network device that you buy. SNMP functionality monitors device statuses and also generates alert messages.
All of these sources are essential inputs to your SIEM system. However, they all record events through different messaging and coding standards and their storage formats are not compatible. So, a data collector that can put these messages into a standard format for processing is essential.
Event message protection
Although the circulation of event messages is a prerequisite for SIEM and not within its competence, the protection of log messages is part of SIEM’s responsibilities. There isn’t much point guarding access to log files if all of the records that go into them can be intercepted and altered before they reach the log server.
Fortunately, the latest versions of status message protocols all include transmission protection procedures. Make sure that the message collector that you deploy is compatible with those standards.
Log message interpretation
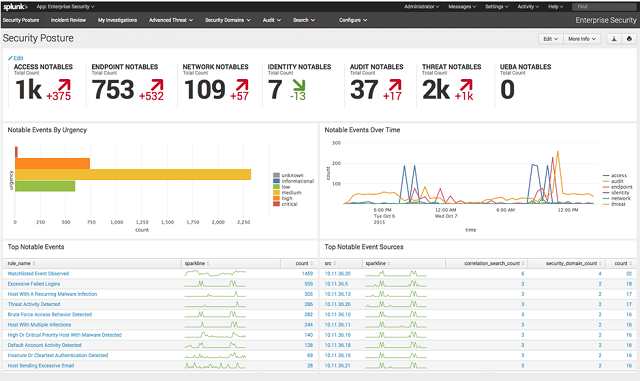
The SEM aspect of SIEM requires that those event messages get interpreted into alerts that are presented to human users in a comprehensible format. These alerts are usually listed in a dashboard panel and the use of color coding for alert severity is very common. The use of line graphs that show performance over time is another useful feature.
Network topology maps that include color coding for devices and links can also speed up event recognition. A facility to get notifications sent outside of the system to key staff also gets essential human resources onto the case immediately. The SEM function of alerting is invariably a live activity. However, those alerts also need to be written to log files in a format that the SIEM console can read back later.
Log file rotation
Log files get very large very quickly and so “log rotation” is an important task that needs to implemented in order to keep individual files down to a manageable size. This term refers to rules that tell the log file creation software to close down a file and create a new file at specified intervals. A very common approach to log file rotation is to create a new file for each day. So the log management program will keep writing to the same file until midnight and then create a new file and write to that.
Other file divisions that can be deployed on large systems write separate logs per message source/device type or network segment.
Log file management
Log files should have meaningful names that relate to their contents. The date is an essential element in file naming. However, another legitimate strategy is to push the date of logs to the name of containing folders.
The file structure of the storage system for logs also needs to have a logical tree layout and a standardized naming convention.
The combination of log message source and date implement one as the folder name and the other as the file name makes access to specific information a lot easier.
Log files need to be retained for a long time – the exact data retention period is specified by the data integrity standard that you follow. However, there is a cut off date between live files and archived files. Archives can be stored in compressed formats and also stored on separate storage media. However, live log files should be uncompressed and accessible from the SIEM dashboard.
System file integrity
It is essential to keep your event logs and other important security files and databases protected. As well as event logs, data sources that need to be protected from tampering include authentication system data, such as Active Directory or LDAP databases, DNS and DHCP server records that control network addressing, and device configuration images.
Any file integrity system should have three lines of defense: access protection, backups, and tamper detection.
The access protection of your log files should just be down to password protection for the directories that contain them or user authentication for databases. Ensure that system access passwords are changed regularly to block access to file storage servers.
Keeping backups of all files can be very storage intensive. Log management requires a lot of capacity just to keep one copy of all of the event messages that your SIEM will collect. Look into SIEM systems that optimize the backup process to minimize backup storage. You can use data compression for backups and you can also implement a policy of only duplicating altered records. Make sure that backups are kept at a different location.
File integrity checks are at the heart of host-based intrusion detection systems (HIDS).
These systems constantly check on the metadata of log files, including version numbers, file size, and last update date. Unmanaged changes in any of these factors trigger a rollback to the last authorized version of the file. Although this strategy increases storage cost because of full file duplication, storage space costs very little compared to the loss of income that intrusion and data breaches can cause. HIDS file protection software is relatively cheap and there are even very comprehensive tools available for free.
Network configuration management
Network configuration management is a borderline SIEM responsibility. Although the actual configuration of network devices is a network administration task, the protection of configuration image files, the standardization of configurations, and the detection of unauthorized configuration changes are part of SIEM.
If you have a large network with many switches and routers, you need to define standard settings for each model and replicate those when new devices are installed. This task requires those standard settings to be stored. Device configurations can be saved to a file, called an image. Those configuration images then need to be stored in a safe place that has all of the file integrity protection procedures outlined in the previous section.
Just as hackers and Trojans routinely try to alter log files to cover their tracks, the alteration of device settings to ease access is another typical intrusion strategy. Therefore, you need to keep an eye on those settings. Unauthorized changes will indicate intruder activity and they need to be rolled back as quickly as possible.
Security weaknesses can be introduced into device settings through human error by a technician accidentally changing a setting. Whether irregular settings changes are performed by unauthorized or authorized access, they need to be rectified.
A comprehensive network configuration manager will repeatedly check network device statuses, usually through SNMP methods. When settings changes are alerted, the config manager will automatically copy over the backup image from storage and rollback those changes.
File transfer protection
Backing up files and restoring them engenders file transfers. It is better to keep backups on a different server, and even on a different site to the location of the original files. This is because you don’t only have intrusion and virus attacks to contend with, you also need to guard against physical access violations, theft of equipment, and environmental damage at your main site.
Your SIEM system backups will require you to send files across the internet, which introduces security risk. Only use secure file transport systems, such as SFTP, FTPS, or SCP when transferring your log files for back up or bringing them back to restore corrupted data or settings. Although the Trivial File Transfer Protocol (TFTP) is often used within LANs for configuration file and log file transfers, switch to a strategy of only using secure file transfer systems even within your network.
File encryption during transfer has the added benefit of not only protecting your data from snoopers but it also alerts you to corruption caused by system glitches or environmental interference. Corrupted encrypted files cannot be decrypted, so you will know to transfer the file again before you use an unreadable file to overwrite your original data.
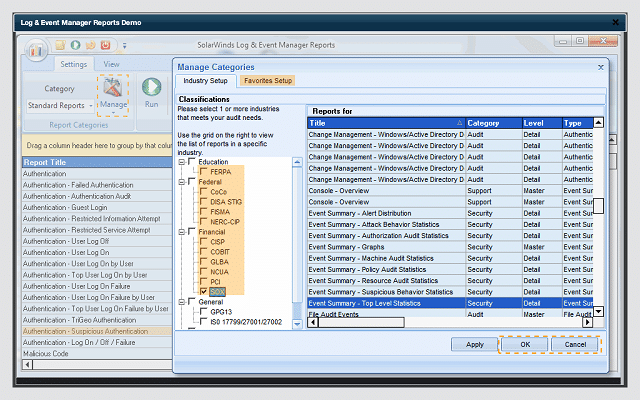
Compliance reporting
Data integrity standards are very commonly implemented and have become essential for any businesses. Data services providers obviously need to give data protection assurances to their customers. However, the protection of data is now a legal obligation for all types of business. This is particularly true in Europe where the leakage of any form of personal information can have serious legal and financial consequences under the General Data Protection Regulation (GDPR).
Data integrity standards offer businesses both a contractual shorthand and a guideline to follow. The listing of data security requirements in a modern service contract would extend to too many pages. It is just simpler for the two parties in the agreement to pick a security standard and write its compliance as a contractual requirement.
Making up your own security procedures is a haphazard strategy and completely unnecessary, thanks to industry standard data protection guidelines. There are many standards organizations out there, but most of them are organized by industry bodies, so the one that is relevant to your business should be relatively obvious.
Here is a brief list of data management security standards that are currently in operation in the English-speaking world. For brevity, these are listed as abbreviations: PCI DSS, HIPAA, SOX, ISO, FISMA, FERPA, NCUA, GLBA, NERC CIP, GPG13, DISA STIG. There are actually many more.
A helpful aspect of picking one of these standards to implement on your site is that they are widely-known and SIEM tool producers particularly tailor their products to one or many of these standards. It is a marketing advantage to them to get the tools certified by the standards bodies and it helps you cut out a lot of research when implementing standards compliance.
Standards compliance requires automated auditing. Once again, those audit processes need to write logs to file, so you end up with logs about logs and those files need to be backed up and retained for a number of years. Standards compliance increases your storage space requirements. However, if you make sure you have a SIEM system that is certified by your chosen standards body, all of that extra file management will protect your business from disastrous data loss or corruption.
Threat intelligence
SIEMs and intrusion detection systems (IDSs) require a threat database in a very similar way that an antivirus program refers to a list of known virus signatures. Just as antivirus program get frequent database updates, a SIEM system needs to add to its database of threat strategies and signatures in order to spot anomalous behavior in the constantly-shifting landscape of cybersecurity.
The threat mitigation modules of SIEMs are becoming increasingly sophisticated and blur the definition boundaries between SIEM and IDS. Top-end SIEM tools will integrate AI to accumulate attack knowledge. Sharing of attack signatures between sites is another strategy that is becoming common even among free tools. Cloud-based SIEM services have a distinct advantage in threat intelligence because knowledge acquired in the defense of one system is instantly available to other customers.
Threat intelligence extends beyond the digital realm because some defense strategies may require the alteration of business procedures. Some SIEMS can produce recommendations for process and workflow adjustments to help you tighten security. Subscription-based SIEM providers also circulate threat alerts to customers and include vulnerability assessments in their services.
Systems administrators can acquire threat intelligence by keeping up-to-date with the developments in SIEM technology, recent attacks, and industry advice through online cybersecurity guides, such as this one.
SIEM consoles
You don’t have to stick to one unified SIEM tool. Many SIEM tools follow common data format standards, so they are interchangeable. Some SIEM tools have fantastic log file management routines but a terrible front-end. There is nothing wrong with using the data collector of one tool, the processor of another, and the dashboard of a third. Some SIEM providers intentionally produce their tools in a modular format, realizing that some users will be very willing to use one feature, while eschewing other utilities in the package. So, no matter which SIEM system you chose, don’t feel trapped into sticking with the console that comes with it.
Dashboard features that you particularly need to look for include:
- Customizable layout
- Color-coded graphical content
- Live data input channels
- Data viewers for viewing log file records
- Analytical tools
- Alert highlighting
- Alert forwarding
Although there is a tendency among systems administrators to stick with command line tools to demonstrate their expertise, graphical user interface usage shouldn’t be seen as the sign of a weak technician. SIEM systems generate such large quantities of data that many text-based searches with regular expressions will slow you down and won’t give you the data summaries that you need to keep on top of threat protection. The console that you use to interpret raw data can make a big difference in your ability to act quickly.
SIEM implementation and extension
Your SIEM should detect anomalous activity and help you spot intrusion. However, this information is only of use if you are prepared to act on it. You need to extend SIEM to attack mitigation strategies, intruder eviction and blocking, and improved authentication procedures. Luckily, you don’t have to manually force users off the system and watch to make sure they don’t try to get back in again. Intrusion prevention systems (IPSs) extend SIEM and automate threat remediation and data restoration for you.
A commonly-reported problem often encountered with newly-installed IPS systems is that they can trigger lockdowns that shut down the business. A straightforward SIEM is just a log management system and shouldn’t interfere too much with your daily business operations.
However, when you extend your SIEM into automated intrusion prevention procedures, you need to be careful that the system doesn’t interpret any system or file access anomaly as a security breach. For example, you have to expect that some users will regularly type in their passwords incorrectly. However, you don’t want to be so loose with your event alerts that you don’t flag repeated failed authentication attempts.
Start your implementation with a straightforward event message reporting tool and build up from there. Once you have your SIEM tool set up with a log file manager and a dashboard for live data viewing, tailor the front-end to filter out standard event messages and focus on critical conditions. Once you understand how to manipulate the source and severity signals of your SIEM, you can start to look into expanding its rules database and subscribing to signature database updates.
Only add machine learning and automated mitigation procedures once you have mastered the basic SIEM system. Security software takes time to understand, so don’t implement more functionality than you can cope with. Implement SIEM progressively and follow on through to a full intrusion prevention system.
SIEM tool recommendations
For this guide, we have tracked down and assessed some great SIEM tools. Not all of these are comprehensive SIEM systems. However, as you will read, each of these tools does what it does exceptionally well.
The market for SIEM tools is very well-supplied and you will be spoilt for choice. However, you probably don’t have a month to set aside from your system administration tasks to fully concentrate on researching and assessing every SIEM tool available, so we have done the legwork for you.
Here is our list of the best SIEM tools for 2019:
- SolarWinds Security Event Manager (FREE TRIAL)
- ManageEngine EventLog Analyzer (FREE TRIAL)
- Papertrail (FREE PLAN)
- Splunk
- OSSEC
- Logstash
- Elasticsearch
- Kibana
- Trustwave SIEM Enterprise
- Nagios Log Server
You can read more about each of these options in the following sections.
1. SolarWinds Security Event Manager (FREE TRIAL)
SolarWinds produces a comprehensive range of network management tools and its professional log management tool is world class. The Security Event Manager runs on Windows Server, but it is able to collect log messages arising from any operating system.
The SolarWinds Security Event Manager will keep tabs on your log files to alert you if any of them get tampered with. This prevents intruders from covering their tracks by deleting log file records. Another security feature of this tool includes a facility to manage memory stick storage.
The name of this tool is a little misleading because it has a lot of features that market it as a SIEM system rather than just a log manager. The tool will present live log messages in the dashboard and it is also possible to read data into the dashboard from stored files. The data viewer includes analysis functions, so you can look for repeated events such as serial failed login attempts.
The reporting tool that is built into the Security Event Manager ships with pre-written report formats that comply with a number of data integrity standards including HIPAA, PCI DSS, SOX, ISO, NCUA, FISMA, FERPA, GLBA, NERC CIP, GPG13, and DISA STIG. The Security Event Manager is suitable for large networks and it is available on a 30-day free trial.
A much cheaper SolarWinds log message manager is the SolarWinds Log Manager for Orion. This shows live log messages and also access log file data for analysis. This tool installs on Windows Server.
The Log Manager for Orion is specifically aimed at customers who already use SolarWinds infrastructure management tools, which are all written on a common platform, called Orion. You can get a 30-day free trial to try it out.
Another SolarWinds log management tool is the Kiwi Syslog Server. This collects Syslog Messages and also SNMP system data. New messages are shown on the dashboard as well as being written to file. It also highlights SNMP alerts, which makes it a lightweight network management system. A nice alert feature is that Kiwi will send you a daily email containing an event summary.
Alerts can be customized to display on volumes of data such as a count of messages reporting a specific event, like failed login attempts. The alerts can also be set to notify you of unusual traffic patterns or traffic surges.
The Kiwi Syslog Server is free to use on networks that include up to five devices. The software installs on Windows Server and you can download it as 14-day free trial.
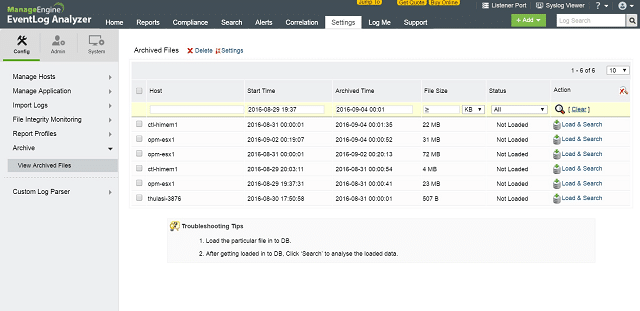
2. ManageEngine EventLog Analyzer (FREE TRIAL)
ManageEngine producers some great infrastructure monitoring tools. The EventLog Analyzer integrates well with the company’s other products. However, it can also be used as a standalone tool. All ManageEngine tools run on Windows or Linux.
This log analyzer gathers Syslog messages and also employs SNMP procedures to monitor network device health. The Syslog messages aren’t just examined for their content, but the Log Analyzer gathers their metadata as well to work out where the message originated.
This a full SIEM tool because you can operate on live data in the dashboard and also set the system to store records to file and read them in for analysis later. Both live and stored records can be manipulated in the data viewer of the dashboard through sorting, search, filtering, and grouping utilities.
The security of log files is enhanced by compression and encryption. Only authorized users are allowed access to files, which goes a long way towards preventing tampering as long as your users’ accounts don’t get compromised. Although the protection of files is pretty comprehensive, EventLog Analyzer also monitors the checksums of log files to alert to any unauthorized alterations to their contents.
The system administrator can create many user accounts to permit access to the system. The dashboard can be locked down to viewing and reporting functions, limiting intervention control access to just a few trusted users. These features are essential for data protection standards compliance.
The framework of this tool was written to provide built-in compliance auditing for the PCI DSS, FISMA, HIPAA standards, and others. You can activate compliance alerts for a specific standard and also access a report set that is specifically written to conform with the requirements of your chosen standard. This is a paid product, but you can use it for free to monitor up to five devices. You can start with a 30-day free trial download.
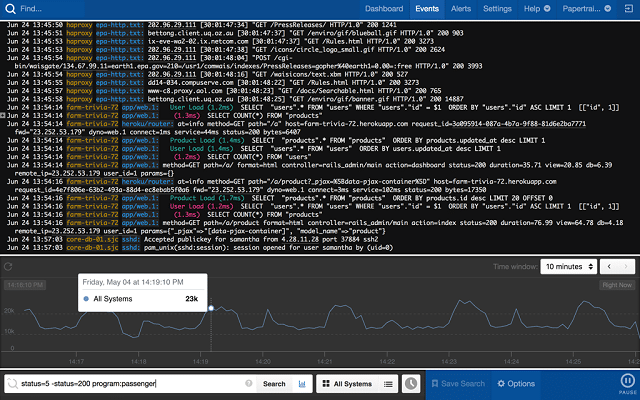
3. Papertrail (FREE PLAN)
Papertrail Log Aggregator is produced by SolarWinds. This useful log management tool will help you centralize your log file storage system from several sources. The major difference between Papertrail and the three SolarWinds log management tools explained in the previous section is that this service is cloud-based. It is accessible from any operating system through commonly-used browsers. The interface for the tool includes record filtering and sorting capabilities that will enable you to perform data analysis – this capability gives Papertrail SIEM capabilities.
The log sources that Papertrail gathers include Windows event logs, Syslog messages, Ruby on Rails program messages, Apache server log files, and router and firewall notifications. Information taken from your network devices via SNMP messaging also gets included. Data collected from your network is uploaded to the Papertrail Cloud servers. You access this data in real time through the browser-based dashboard. Data transfers, storage and access are all guarded with encryption. Only authorized users are allowed access to your company’s data stored on the server and you can set up an unlimited number of user accounts.
Dashboard utilities include performance and anomaly alerts that are based on the detection and intrusion signatures stored in the Papertrail threat database. Instant threat alerts based on live data can also be added with combinations of conditions and customized warnings.
Papertrail will also store your log data, making it available for analysis. These capabilities provide the SIM part of SIEM.
Archiving of log files also takes place on the Papertrail server, so this deal is a combined log analysis and cloud storage package.
The charging structure of Papertrail is by subscription and the lowest plan is free to use. The higher plans give you longer archive storage periods and the period of data that you access for analysis also lengthens. As well as pre-set service plans, Papertrail offers a customizable plan. You set your own monthly upload allowance and the periods for analysis and archiving in the subscription rate calculator. Check on the archiving requirements of any data integrity standards that you follow before setting these custom plan variables. The plan flexibility of Papertrail makes this a very scalable SIEM service that is suitable for all sizes of networks. You can register for the free plan to try this product out.
4. Splunk
Splunk is a very widely-used log file management system that qualifies as a SIEM. The system is available in three service levels. The lowest package is a SIM because it doesn’t include any operation on live data, which means it isn’t able to show you live alerts. This is Free Splunk and it can only deal with data take out of log files. However, that situation is very easy to manipulate in order to give yourself alert notification through Free Splunk – you simply channel those alerts into a file and then out to the Splunk front-end.
All levels of Splunk run on Windows, Linux, and macOS. There is also an online Software-as-a-Service (SaaS) version. The highest plan is a fully comprehensive network management system that even includes comprehensive automation, called the Adaptive Operations Framework. This system allows you to enable suggested remediation to kick in upon threat detection. This makes that version, which is called Splunk Enterprise into an intrusion prevention system.
All versions of Splunk include a data analyzer. This enables you to sort and filter records that are read in from files. You can also write out to new files from the analyzer. With the higher levels of Splunk, that analysis can be applied to live data. This enables you to filter out the less important warnings to prevent the dashboard from getting too busy.
The data viewer for both live and stored records has a great data abstraction facility that makes it a data mining tool; you can drill down from a top-level anomaly grouping to see down to individual messages. This organizational feature provides alert summaries that make a systemwide overview much easier to comprehend.
A module, called the Asset Investigator shows alerts from a device perspective and produces action recommendation that will help you block any attack on that device from being repeated.
5. OSSEC

OSSEC is a leading host-based intrusion detection system and it is completely free of charge. As a HIDS, it is mainly-driven by log file analysis, which would normally make this a SIM. However, the tool also monitors any actions on a number of key system resources in real time, giving it SEM capabilities.
The only shortfall that prevents OSSEC from being regarded as a leading SIEM tool is that its front end is not very good, and in fact is no longer supported. So it only offers you a complete SIEM solution in conjunction with other dashboard data viewing and analytical tools, such as Splunk, Kibana, and Graylog.
The code for OSSEC is open source and the utility is free to use. The system is actually owned by a company, Trend Micro, which doesn’t charge for it. The downside of a free system is that you don’t get professional support for it. However, there is an active community for the tool, which communicates through a forum, and Trend Micro offers professional support packages for OSSEC for a fee.
There are versions of OSSEC data collectors for all the major operating systems: Windows, Linux, Unix, and macOS. The developers cleverly included adaptable capabilities so the installation will perform differently according to the log protocols generated by each operating system.
It will pick up Windows event log data and it will also monitor changes to the registry on Windows. On Unix, Linux, and macOS, OSSEC logs any access to the root account. In all operating systems, the tool keeps a check on log file checksums to alert any tampering attempts. Backups that occur upon logfile alteration enable OSSEC to rollback and overwrite unauthorized changes to those files.
All data gets centralized in a central management system, which includes a file manager as well as a data processor. Unfortunately, this module can’t be installed on Windows, only Unix, Linux, and macOS.
OSSEC collects log data from email systems, FTP, and Web servers. It also monitors firewall and antivirus logs and tables, operating system event logs, and traffic logs.
The rule base of OSSERC is a series of “policies.” Each policy is an anomaly signature, which, when detected, triggers an alert. You can find free sets of policies in the community forum or write your own.
6. Logstash
Logstash is a log file creation facility produced by the Dutch company, Elasticsearch BV. The company takes its name from the first SIEM product that it created, which you can read about in the next section.
The company completed its SIEM tool product list by adding two more utilities to Elasticsearch. Logstash is one of these. The three tools work together to create a full SIEM system. However, each individual module can be used in conjunction with tools produced by others. So, individually, each of these three products can be regarded as SIEM software, put together, they form a SIEM system. The company refers to this suite as the “Elastic Stack.” All of the Elastic Stack modules are open source and free to use.
Logstash provides the bottom layer of the stack. It collects log data from the network and writes them to file. The tool consolidates log data from disparate sources and fits them into a neutral format to form log file records of the same layout. You can specify in the settings of Logstash which types of records its should gather, so if you want to, you can intentionally miss certain sources. This would be a meaningful scenario if there were certain log messages that you wanted to keep separate from the rest.
Logstash will rotate logs by data, or source and also generate a meaningful file storage directory structure.
Although the system has its own record format, the Logstash file interface can reinterpret them into other formats for delivery to a long list of data viewing utilities. Even though this tool was specifically written to support Elasticsearch, the developers also wanted to provide interoperability with other SIEM tools. The tool can also collect data from and send data to AWS and Azure Cloud services.
The Logstash data collection functions can be set to run data through files and out to a console immediately. This flow of data from collection through viewer is called the “ingest-to-visualization pipeline.” It will give you near-live views on log data.
7. Elasticsearch
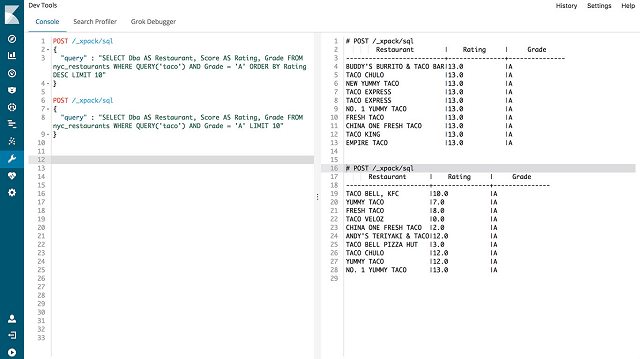
Elasticsearch, a free, open-source SIEM utility, is where the Elastic Stack began. The purpose of this tool is to search and sort through several different log files and compile unified records in a standardized format. The file search facility will execute your queries to extract matching records from a whole tree of file directories, implementing grouping and aggregation on demand.
Elasticsearch is a great tool for data exploration and analysis. Logstash was created to provide an order source of files for Elasticsearch. However, this data querying tool is capable of searching through unconsolidated log files containing records in the standard formats of their original sources, so you don’t have to implement Logstash in order to use Elasticsearch. You can combine this tool with any other log server system.
The Elastic Stack layered approach means that Elasticsearch, which is the middle layer of the stack, was designed to be used by more sophisticated dashboards. The module’s program package includes a query language that many front-ends can communicate with. It includes an API to enable the streaming of data back to a querying console. The tool has interface clients that operate in many different programming languages, including Java, Python, PHP, SQL, and .NET.
Although Elasticsearch can interact with many different data viewing and analysis tools written by third parties, Kibana was written specifically to interact with this tool.
8. Kibana

Although it wasn’t the first tool written for the Elastic Suite, Kibana is the star of the Stack. This is a very powerful data viewing and analysis tool. It is free and open source and it was written to interact with a lot of data sources. It is the most frequently used front-end for OSSEC. In fact, all of the usage snapshots on the OSSEC website show Kibana. This is a top pick SIEM dashboard utility.
Kibana has its own command language and the interface includes a script editor, so you can write your own routines to fetch and represent data. If you don’t have any interest in writing a program, you can also read in data and organize it into data panels and visual representations through point-and-click methods.
Not all data sources will be as well-organized as those provided by Logstash, if you read in data from files that aren’t rotated by source or data, you can limit the data load in Kibana to just one segment, e.g., by date. If you don’t have an efficient log file management system, you can reorganize your files by processing them through Kibana.
The interface includes a raw data viewer, so if you find it difficult to believe the information that some of the graphs in the dashboard are showing you, you can always go down to the original records for confirmation. Those visualizations include time series graphs, pie charts, scatter graphs, and map views. Records can be sorted, filtered, and grouped for analysis.
The dashboard is completely customizable and any panel can be printed out as reports. You can schedule reports to run periodically or get them on demand.
Kibana is a great free SIEM tool. Unfortunately, it is only available for Linux.
9. Trustwave SIEM Enterprise

Trustwave produces its SIEM service both as software and as a network appliance. This service has very strong security procedures and includes a number of threat and signature databases that dictate how the SIEM searches out anomalies and generates alerts.
The dashboard of SIEM Enterprise loads into a browser, so you can access the interface from any operating system. As well as showing alerts on the screen, the dashboard will give you recommendations on actions that should be taken to address the identified threat. Additionally, you can switch to the data viewer and search through records automatically for log records that related to the highlighted event. These services all operate on live data.
The company also produces Trustwave Log Management Appliances, which add SIM capabilities to your SIEM suite. You can write log files out from Trustwave SIEM Enterprise, but this manual solution isn’t feasible for large networks. The tool is able to collect data from many points in the network, giving you simultaneous views on activity. This is particularly useful for large networks. However, it does generate large amounts of data. The data management tools in Trustwave SIEM Enterprise assist you in the management of all of this information by highlighting what’s important and allowing you to filter out everything else.
This is a good tool for standards compliance and it includes a number of audit features. These include control monitoring to record the access to sensitive data and also reporting that conforms with many security standards. You can set compliance alerts to keep you inside the parameters laid down by the standards that your business has chosen to follow. Of the 2,600 standard report formats that ship with the tool, 600 are specifically designed for standards compliance.
Although this is a very comprehensive SEM system, you would need the SIM functions of the Trustwave Log Manager in order to get the full suite of SIEM capabilities.
10. Nagios Log Server
 –
–
Nagios is a popular network management system. It is available in a free version, called Nagios Core, and a paid version called Nagios XI. Nagios Core is an open source project and so its code has been used as the basis for many other network management systems. A companion utility that is available from the Nagios group is the Nagios Log Server. This is not an open source project; however, the software is free to use if you have a log message throughput of no more than 500 MB of data per day. Larger systems have to pay for the Log Server.
The Nagios Log Server runs on Windows and Linux. It gathers Windows events as well as Syslog data. Although this is billed as a log management system, it is more than a SIM because the records pass through a data viewer dashboard as well as getting saved to file. This gives you SEM capabilities and offers you the full SIEM requirements of both live operations and storage mechanisms for system messaging.
The log file manager offers storage configuration options. You can choose to centralize files and keep them in one central location, or operate a distributed storage architecture. Either way, the Log Server manages access to stored records as well as saving them in an orderly structure.
The log manager can be configured to filter out lower-level warnings and only write higher alerts to file and it can also parse records according to source. You can set the file rotation by date to keep your logs files of manageable size.
Distributed file access has the advantage of limiting the potential damage that access to one file store could bring and it also reduces the risks of environmental damage to the equipment held in one particular location. However, it doesn’t eradicate physical or access threats entirely because any partial loss of log data can be very damaging. So, you have the option of creating backups of all log files whether you opt for centralized or distributed storage.
The dashboard gives you access to live data and you can sort, search, filter, and group it. There are a number of visualization options in the data viewer that will help you recognize system statuses instantly. You can also load data from files to use the data analysis tools on a longer set of historical data.
This SIEM solution is very attractive but it is priced at the high end of the market even though it doesn’t have the auditing and standards compliance policy enforcement that other tools on this list include. This is why the Nagios Log Server is number ten on our list of recommendations.
Implementing SIEM
Hopefully, this guide has given you all of the information that you need in order to implement SIEM on your network. Terminology sometimes obscures meaning rather than clarifying it. After reading the explanation of exactly what SIEM involves, you might recognize some of the functions and realize that you have already implemented much of these practices and have a partial or even a full SIEM system already in operation under another name.
It is highly likely that you already have log file management software in place. If you have that capability as a free extra to some other utility, such as your network monitoring system, then make sure you turn it on. Look in the dashboard of any network systems that you already have to see if it has data analysis features that will enable you to read in log files and investigate them. Certainly, the SIM aspect of SIEM is more likely to already be on your network than the SEM live data functions of the field.
Check out the data protection standards that are required in your industry and pick a SIEM system that enforces it. Calibrating your system alerts to the parameters required for standards compliance can be time-consuming and prone to error, so finding a SIEM system with pre-set alerts to fit in with your standards compliance needs wipes a whole lot of work off your desk. Similarly, pre-written auditing procedures and report formats in your SIEM tool will save your company a lot of time and money.
Do you use a SIEM tool already? When you started your SIM implementation project, did you discover that you already had much of the required functionality available in your existing management software? Do you filter out messages before they arrive at the log file?
Do you find you sometimes get overwhelmed by the sheer volume of log data that you need to store for compliance? Leave a message in the Comments section below to share your experience with the community.



SIEM items have turned into a centre piece of distinguishing and tending to digital assaults. As this tool interface can be used with many programming languages it become easy to use it. It’s 360 degree protection feature is worthy and useful to work on.