The management of user permissions on networks is dominated by two systems: Active Directory (AD) and Lightweight Directory Access Protocol (LDAP). Active Directory is only available for Windows environments and it is at the heart of access control for a range of Microsoft product, including the Microsoft Exchange email server.
LDAP is a protocol rather than an application. That means that it is a set of guidelines and not a product. So, there are many implementations of LDAP for a range of operating systems. However, as AD is integrated into Windows, it is the most widely-used access management system on that platform. Without the availability of AD, Linux systems rely on LDAP.
>>>Jump to the list of best Access Management tools and software below<<<
Contents
About Active Directory
Active Directory, or AD, is part of the Windows Server operating system. It forms part of Windows Server 2000, Windows Server 2003, Windows Server 2008, Windows Server 2012, Windows Server 2016, and Windows Server 2019. The utility is a directory service for the network. It is a database that includes user privileges and authorization data. The core of Active Directory is called Active Directory Domain Services. This allows access to the authorization and authentication details in the database through an API that allows access to the data through a set of dedicated commands and functions.
In Active Directory terminology, a domain is a group of computers connected together on a network and administered by one authentication server. The Active Directory utility that controls access to resources on the network is held on the authentication server. The server supporting this facility is called the Domain Controller, or DC. Active Directory has a replication architecture. This means that copies of the same directory are held on more than one server. If information is added or updated on one Domain Controller it will propagate these changes to the other Domain Controllers in the system.
A wider area than the domain in Windows Server terminology is the “forest.” The forest is the total network space covered by a group of communicating Domain Controllers. One business may have many forests, each containing many Domain Controllers. Users in one forest would need to have separate authentication rights to access resources on another forest, even though that forest may be owned by the same company and connected to the same network. By this method, network administrators are able to create separate security zones within a single local area network.
User credentials with Active Directory
When you log in to a network controlled by Active Directory, your credentials are checked against the copy of the global catalog held in your local Domain Controller. This process not only sends your username and password to the authentication server, but the details of the computer from which you logged in. This means that environments operating a “bring your own device” policy create extra work for the network administrator who has to create authorization data for each employee-owned device accessing the network.
A user may be denied access even though his username and password are correct and recognized by the Active Directory Domain Controller because his computer does not have permissions to access the network.
The replication process of Active Directory helps maintain accurate copies of the global catalog on each Domain Controller in the forest. This procedure occurs every 15 minutes with all the DCs sending copies of their directory to their peers. Some events, like a lock out for too many incorrect password attempts, invoke immediate notification of all DCs.
Many Microsoft products employ Active Directory for user authentication. The most significant of these is Microsoft Exchange, an email management system that runs on Windows Server. Exchange runs its own separate AD system. However, this can be rippled through by connecting the Exchange AD implementation into the forest operating in the business.
About the Lightweight Directory Access Protocol
LDAP has been around longer than Active Directory. In fact, Microsoft based its development of AD on a number of existing protocols, including LDAP. The LDAP specifications were first published in 1993 and it was based on an even earlier authentication system, called X.500. This makes LDAP one of the oldest protocols in use on networks today. The specification has been updated twice and the current version is LDAPv3.
The importance of version 3 is that it adds security protection for LDAP communications. Before this version, all LDAP messages were transported around the network in plain text. LDAP now uses Transport Layer Security to protect messages, so the system can be used safely over the internet. This secure version of LDAP is sometimes called LAPS or LDAP over SSL. The Kerberos encryption system can also be used to provide security for LDAP messages.
Like AD, LDAP can be used as a distributed authentication service. The cluster of servers update each other through a replication procedure.
LDAP messaging can be carried out using web-style addressing. Rather than the commonly known “http://” scheme, LDAP addresses begin with “ldap://.” The addressing system includes query components, which enables all referencing actions to be performed with one call. This communication method is not universally implemented.
LDAP implementation
The permissions database of LDAP is stored in a tree layout, which is called the directory information tree (DIT). Each entry defines an “object,” which can be a person or a resource, such as a PC. This gives LDAP a great deal of flexibility, which enables it to be deployed in a range of different directory scenarios, not just for authentication purposes. Access to the Domain Name Service (DNS) is managed with LDAP procedures. This is an adaptation of the standard purpose of the protocol, which is to provide authentication information.
It is possible to create object classes, which makes it easy to apply access rules to groups of devices or people. The protocol doesn’t specify how the service should be implemented, it just defines the language used for communicating with the server and the storage structure. So some implementations store permissions records in a flat file while others involve inserting authentication data into a database.
Not all records need to be held in every copy of the database in a distributed environment. In these cases, LDAP employs a forwarding mechanism that sends queries on to the location of the required data. This is best illustrated by the way the DNS system works. The most frequently-used references can be stored locally, so addresses can be stored at the network segment level. If a user requires access to a remote resource, the local LDAP server will push the access permission query on to the database that is local to that resource.
Access Control List
Access Control List, or ACL, is a rival directory service mechanism that is sometimes used for access management. ACL is not nearly as widely implemented as AD or LDAP, but it is available in a number of network products and services, such as the Network File Server (NFS). ACL is not used for the authentication of personnel but is intended to guard access to resources. The integration of ACL into NFS is probably the most widely-used implementation of this access control methodology. A big advantage of ACL is that it can be used on just about any operating system.
An ACL permissions file contains a series of entries for the resources being guarded. So, if the access control were to be placed on a file, the “object” would be the name of the file being protected. Each file record starts with the object name followed by a list of users who are allowed access. Each user in the list is followed by an access level, such as “read” or “write.” The standard permission level set is different according to the object type. ACL provides the file access system for the blogging platform, Joomla.
Access Management deployment
The above access management directory services are not intended for use directly by human users. The maintenance and reference of these directories is meant to be carried out by other applications. Therefore, in order to implement an access management system for your resources, you should look for an Identity and Access Management (IAM) package.
Identity and Access Management systems
You probably already employ network management software. Just as network performance monitors exploit the messaging systems built into networking equipment, such as NetFlow and SNMP, IAMs sit on top of the information that is available in access directory services.
In both cases, access permission and network device status messages are difficult to interpret, so the basic requirement of an Identity and Access Management tool is that it should present the directory contents in a comprehensible format.
Extra features that you can expect from an IAM include the ability to set directory storage to be duplicated or distributed. You should also be able to nominate domain controllers that should be independent and those that should be linked.
The IAM should enable you to formulate access policies and create groups for both devices and for individuals. These policies should be rolled out, allowing you to assign a set of permissions to groups of users and you should also be able to access these roles when setting up new users through the IAM interface.
The current regulatory environment requires you to periodically report on data access and so being able to generate access control reports and even user activities will make it easier to complete your compliance reporting tasks.
Recommended access management tools
Access management systems fall into a number of categories. Some comprehensive network management systems integrate access control. These tools are at one end of the range of tools that you could look at; at the other end are simple and lightweight directory interpreters that just help you see and alter the contents of your system permissions.
Here is our list of the best access management tools:
- SolarWinds Access Rights Manager (FREE TRIAL)
- ManageEngine AD360 (FREE TRIAL)
- Apache Directory
- FreeIPA
- LDAP Account Manager
You can read details about these access managers in the following sections.
1. SolarWinds Access Rights Manager (FREE TRIAL)
SolarWinds is a leading producer of infrastructure monitoring tool and this option is by no means the only SolarWinds product that can interact with Active Directory. The SolarWinds Server and Application Monitor is also able to connect to your AD system and help you manage it. That tool can also look after your Microsoft Exchange Server.
If you don’t need a full application monitor and just want a system to manage your Active Directory function, then you would do very well by choosing the SolarWinds Access Rights Manager. SolarWinds only produces software for Windows Server, so you won’t be able to run this tool on a Linux computer. On the plus side, if you run Microsoft Exchange Server, this application can monitor that as well.
If you have Exchange, you probably have its permissions in a separate domain controller for AD than the one that you use for your network and access to other resources including file sharing. That isn’t a problem for the SolarWinds Access Rights Manager because it can oversee all of your domain controllers and your entire AD forest. It can event extend its vision out to Cloud services.
The Manager will keep track of your AD entries and highlight any changes that have been made to them. You can also update, add, and delete records through the manager interface. The Access Rights Manager will produce audit reports to help you demonstrate standards compliance. Analysis functions in the application help you to manage user groups and hone access rights to tighten system security.
The SolarWinds Access Rights Manager is top-of-the-line and high quality costs money, so this tool is not cheap. However, SolarWinds offers the application on a 30-day free trial, so you can assess it risk free.
2. ManageEngine AD360 (FREE TRIAL)
ManageEngine AD360 is a full identity and access management system and it is available both for Windows Server and for Linux. The tool can manage AD implementations for your network resources and also for Exchange Server, G Suite, and Office 365.
As well as being able to access your AD databases, you can edit entries, add them, and delete them. The tool includes an audit trail so you can spot any unauthorized changes to access rights. The tool will pay particular attention to the activities of user accounts with heightened privileges.
The AD360 system can extend its monitoring activities out to Cloud services and it can also manage single sign-on scenarios. These two strategies expose your user accounts to heightened security risk, so the AD360 system enables you to apply multi-factor authentication methods.
Access to the functions in the AD360 screens can be limited and that enables you to create user accounts for junior staff or Help Desk crew to enable you to delegate user account management tasks. AD 360 also includes self-service screens that enable users to create or change their own passwords.
ManageEngine offers a 60-day free trial of AD360.
3. Apache Directory
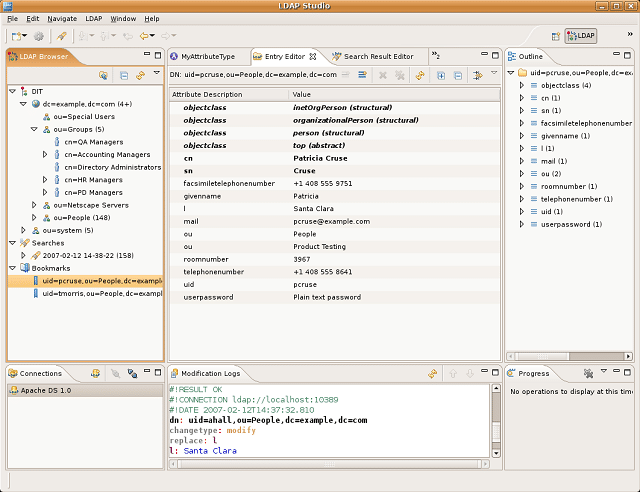
There are two strong reasons why you might not opt for the SolarWinds tool: budget and operating system. If you run Linux on your server, then you would be better off with the Apache Directory. The other draw of this option is that it is free to use. You may need to tweak the software a little to get it working, but as you will be saving a ton of money by going for the Apache service, you could budget for some tech time to get the application installed.
You have probably heard of Apache HTTP Server. In fact, if you have a web server on a Linux system, you probably already have that software. Apache Directory is a separate project so don’t expect the two to integrate seamlessly. However, this is an open source product, just like the server system.
Apache Directory implements LDAP. The management package has two elements, which are a server program that operates the LDAP database and a client that helps you manage entries in the directory. The server module is called Apache DirectoryDS and the client is called Apache Directory Studio. Both elements of Apache Directory can be installed on Windows, Linux, Unix, and Mac OS.
4. FreeIPA

FreeIPA is an IAM written for Linux platforms. The software can be installed on RHEL, Mac OS, and Unix. Although it doesn’t run on Windows, FreeIPA cleverly mimics Active Directory, which isn’t usually available for Linux.
As the name suggests, this tool is free to use. “IPA” stands for Identity, Policy, and Audit. This is an open source project, so you get access to the code to check it through for security issues and you can even adapt it if you have the programming skills available. The directory module of FreeIPA is provided by a standalone application, called 389 Directory Server. That element is also available to be used without FreeIPA. The package includes a client module that gives you access to directory records and enables you to add, alter, or delete them.
The installation package also includes an implementation of Kerberos for encryption and there are also security certificate management modules. There are a number of other elements of FreeIPA which are pulled in from other projects, so this IAM is actually a collection of software developed by different organizations. This strategy has advantages because all of the elements of FreeIPA have been widely-used for some time and they have been thoroughly proven in real world scenarios. A pitfall of the multi-source nature of the tool is that it complicates the process of patching and updating the software.
5. LDAP Account Manager
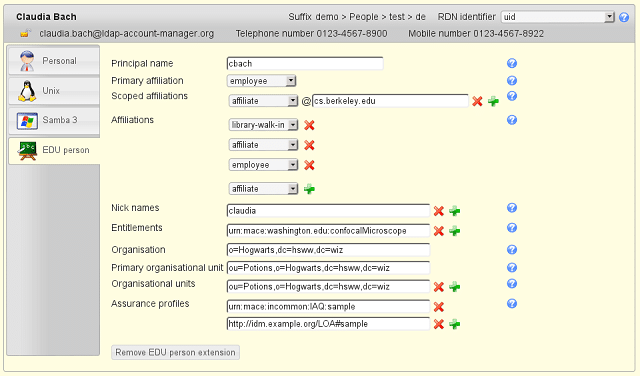
LDAP Account Manager is available for free and there is also a paid premium version. The software installs on Debian, Fedora, and SUSE Linux.
This is a very straightforward tool that offers an LDAP database viewer and editor. That’s about the limit of the system’s functionality.
The paid version of the tool is called LDAP Account Manager Pro. This option includes a self-service option and also a lost password reset feature. You can enhance security with the Pro version by taking advantage of its multi-factor authentication option.
LDAP Account Manager Pro isn’t as sophisticated as the other options on this list. However, it offers the access management features that an enterprise needs and it costs less than its rivals. The free version of this tool would be more suitable for use by a private individual, or a very small business.
Implementing Access Management
Your choice of Identity and Access Management software will be dominated by two factors, which are the dominant operating system that your business’s infrastructure uses and your budget.
Very small enterprises probably don’t have many system users, and so a straightforward directory interpreter should be enough. If you have lots of users, features such as single sign on, self-service, and automated password resetting mechanisms will lift a lot of tasks off the shoulders of your system admin team.
Password management is a big issue both for private individuals and for businesses because it is very common for people to forget their passwords. At the same time, you don’t want to make life too difficult for users, otherwise, they will choose simple passwords or even write them down … and then lose the note.
Although LDAP can be installed on Windows, the probability is that if you have a Windows server, you will be using Active Directory. The fact that this system underpins Microsoft Office and Exchange Server as well as providing network and hardware access controls makes it too important to pass over. Although you might not like being tied to the products of one large software provider, the benefits of AD’s integrations are overwhelming.
If you have a Linux server, you won’t be using Active Directory and you will need LDAP. So, you will need to focus on LDAP-compatible identity and access management tools.
The tools on this list are either free or are available on free trials, so give a few of them a try to see which one you prefer. Do you already have an identity and access management tool operating on your network? Which one do you use? Do you use any of the tools listed in this guide? Leave a message in the Comments section below and share your experience with the community.
Image: Login screen from Pixabay. Public domain.