The cost of data breaches are severe. According to an IBM-sponsored study by Ponemon Institute, the average cost of a data breach is $3.62 million USD. This statistic demonstrates that organizations must take a proactive approach to network security. It also helps explain why sharpening your network security skills can help keep you in-demand in a competitive job market.
A big part of network security is the ability to detect vulnerabilities on your network before someone looking to exploit them does. That’s where network vulnerability scanning comes in. In this article we’ll dive into the basics of network vulnerability scanning and then jump into an overview of some of the more popular port and vulnerability scanners, and security solutions available for Windows, Linux, and Mac OS X today.
Here is our list of the seven best network vulnerability scanners:
- SolarWinds Network Configuration Manager (FREE TRIAL) Standardizes the settings of network devices and then prevents any unauthorized changes. Installs on Windows Server.
- SolarWinds Port Scanner (FREE TRIAL) This port checker is part of the Engineer’s Toolset, which provides more than 60 system management tools. Runs on Windows Server.
- CrowdStrike Falcon Spotlight This cloud-based service offers continuous monitoring of software and references a threat intelligence database.
- Nessus Professional This is a well-respected and widely copied vulnerability scanner that has a free Community Edition. Delivered through a website.
- Vega This free, open source vulnerability scanner specializes in spotting SQL injection and cross-site scripting opportunities. Available for Windows, Linux, and macOS.
- Nmap A free network scanner that can be used to spot anomalous activity that denoted malicious actions. Runs on Windows, Linux, and macOS.
- ZAP Zed Attack Proxy is a free, open source tool that identifies security weaknesses and can be extended by plug-ins. Runs on Windows, Linux, and macOS.
What is network vulnerability scanning?
Network vulnerability scanning is the use of computer programs to check computer networks for known vulnerabilities or configurations that could lead to the compromise of network security. The common use cases for network vulnerability scanning include: establishing a baseline for network security, assessing web servers, and both white and black hat hacking.
There are a wide variety of software products that in some way, shape, or form fit into the “vulnerability scanner” category. Some of the more common features include: port scanning, ciphersuite detection, reporting, the ability to automate scans, and credentialed scans.
Is a vulnerability scan the same as a penetration test?
While similar in their intent to help identify potential weak spots in network security, vulnerability scans and penetration tests are fundamentally different. The goal of a vulnerability scan is to scan the network and report back any detected vulnerabilities. The goal of a penetration test is to demonstrate ways a network could be compromised. Generally, internal IT staff will conduct vulnerability scans while a third party will perform a penetration test. Using a third party for penetration tests helps avoid possible conflicts of interest (e.g. the security engineer may not have incentive to demonstrate the network isn’t secure).
In short, penetration testers may use vulnerability scanners as a means to achieve their end, but the penetration test attempts to go the extra step of actually compromising network devices.
What should you look for in a network vulnerability scanner?
As with most things, you should focus your search for a vulnerability scanner around your specific use case. An organization that must be complaint to regulations like PCI-DSS (Payment Card Industry Data Security Standard), SOX (Sarbanes-Oxley Act of 2002), HIPAA (Health Insurance Portability and Accountability Act of 1996), or GDPR (General Data Protection Regulation) will have different requirements than one that doesn’t. Similarly, an aspiring penetration tester just getting started may have different needs than someone with a few years of experience under the belt.
Using our list below as an example, almost every security professional would be well-served to have nmap skills in their toolbox, while SolarWinds Port Scanner may be a great way for aspiring pros to ease into port scanning. Similarly, the price tag of a tool like SolarWinds NCM or Nessus might not make sense for a team of one or two, while ROI could be huge for firms looking for a scalable security solution.
Regardless of your use case, at a high-level, you’ll likely want to make sure the solution is from a reputable source and includes at least basic port scanning, vulnerability detection, and reporting features. Additionally, if you are depending on a given tool to call out specific vulnerabilities for you, you’ll want to make sure the vulnerability database for that tool is regularly updated.
As you start looking at more advanced solutions, you’ll need to ask if you need features like: configuration monitoring, default password checks, cloud solutions, and data visualization. Similarly, you’ll need to ask if you’re willing to build out the scripts required to achieve this functionality on your own or if you need a platform that has built-in functionality (e.g. SolarWinds NCM & Nessus).
The Best Network Vulnerability Scanners
Now that we’ve reviewed the basics of vulnerability scanning, here is our list of the top vulnerability scanners & port scanners:
1. SolarWinds Network Configuration Manager (FREE TRIAL)
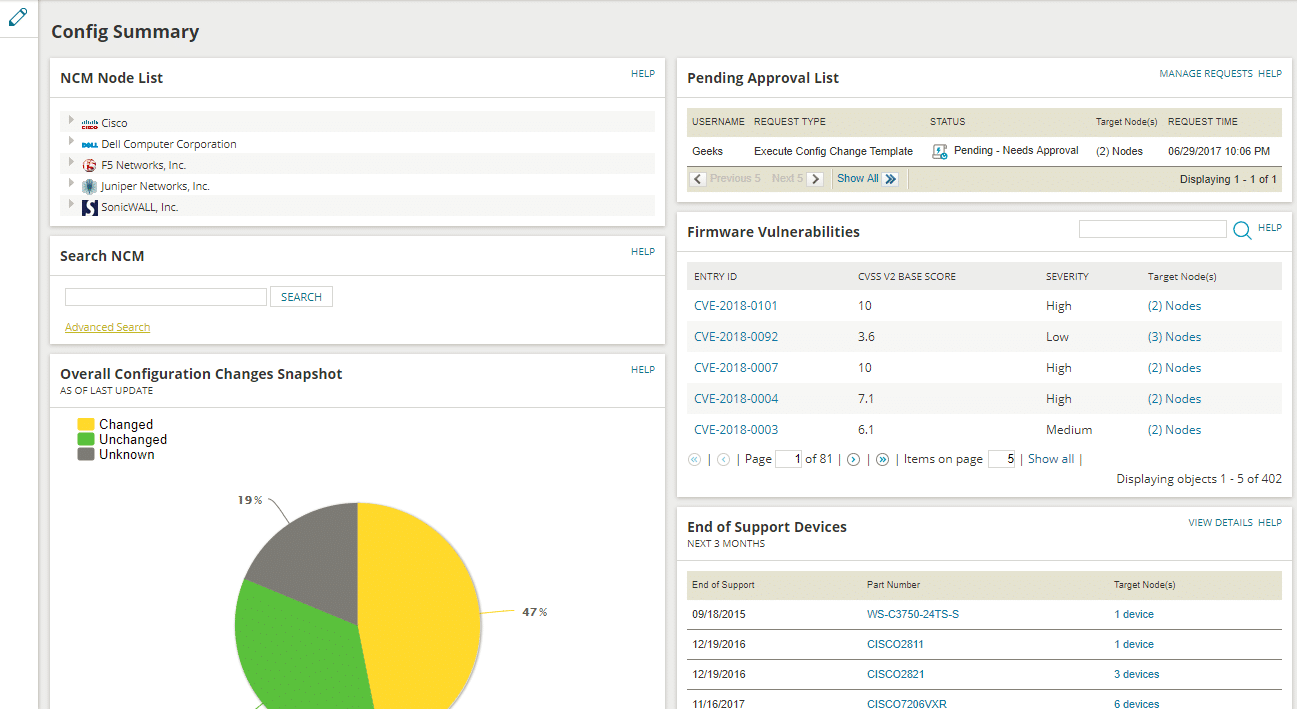
SolarWinds Network Configuration Manager (NCM) is an enterprise solution that enables configuration management, compliance management, lifecycle management, vulnerability assessment, and more. Effectively identifying and mitigating vulnerabilities goes beyond just scanning servers and comparing them to CVE (Common Vulnerabilities and Exposures) details. NCM includes a built-in vulnerability scanner and offers features that help make network security manageable at scale. For example, from the NCM dashboard you can directly approve change requests, view firmware vulnerabilities on the network, see devices that are nearing or beyond their end of support date, and see a visualization of your baseline configurations versus your running configurations.
NCM can integrate with Network Performance Monitor (NPM) directly or work as a standalone solution. You can test drive NCM directly from a web browser; download the free trial here.
2. SolarWinds Port Scanner (FREE TOOL)
In addition to their enterprise-level solution, SolarWinds offer a free Port Scanner tool can help you dive into network scanning. The tool itself is an executable file that can run on Windows operating systems. While not quite a full blown “vulnerability scanner” (it doesn’t detect specific CVEs for example), this tool does enable you to check for open TCP or UDP ports and services and run operating system detection on the network. The simple GUI (Graphical User Interface) makes this tool easy to get started with, and the CLI (Command Line Interface) options add power and scriptability for more advanced users. Scan results can be saved in .csv, .xlxs, or .xml format so you can forward or parse the data as needed. You can pick up your free download here.
3. CrowdStrike Falcon Spotlight

CrowdStrike Falcon Spotlight is delivered from a cloud platform. The Falcon system is a group of tools that can be used in combination. These tools all rely on a system of endpoint agents that perform local research within the network. Those agents upload research data to the platform and all of the services that you subscribe to mine it, looking for threats.
CrowdStrike supplies a threat intelligence feed and that informs the vulnerability searches of Falcon Spotlight. The system assesses activity and software on each endpoint. The monitor is continuous and creates a prioritized action list in the dashboard for Spotlight.
The CrowdStrike system uses AI processes to identify potential vulnerabilities before threats actually arise. You can also subscribe to Falcon XDR to watch your system in case threats arise anyway. You can assess your network requirements with access to a 15-day free trial.
4. Nessus

Nessus Professional from Tenable is one of the most popular network vulnerability scanners available today. Nessus offers comprehensive scanning tools that not only check for open ports but also look for vulnerabilities based on a well-maintained list of definitions. The reporting features in Nessus help make results and recommended action easy to understand and the ability to save scan configurations adds to ease of use.
Additionally, Nessus helps remove some of the complexity of getting started by offering a number of built-in scan templates. The templates help you select scans that are optimized for specific scenarios. Examples include: Internal PCI Network Scan, Mobile Device Scan, Credentialed Patch Audit, and PCI Quarterly External Scan.
Severity scores ranging from 1-10 help you quantify how serious a given threat may be. The ability to correlate data from frameworks like Metasploit and Canvas add an additional layer of extensibility.
If you are looking for a cloud-based solution, Tenable offers Tenable.io a platform that ties together multiple Nessus tools with third-party systems and data.
You can sign up for free trials of Nessus Pro or Tenable.io here.
5. Vega

Vega is a free and open source vulnerability scanner from the Montreal-based Subgraph. The primary use case for Vega is scanning websites for vulnerabilities like cross-site scripting (XSS), SQL injections, insecure cipher suites, and more. If you are a website administrator tasked with making sure your site is secure or a penetration tester focused on web-based services, Vega may be a good choice for you.
The GUI interface makes Vega an easy website vulnerability scanner to get started with. Scan results are relatively easy to understand and include High/Medium/Low/Info level categorizations.
In addition to manual scans, Vega supports advanced features like the Vega Proxy and automated site crawling and scanning. You can add credentials to scans for deeper dives and more advanced testing.
Vega can be installed on Windows, Linux, or Mac OS X. In addition to the aforementioned GUI, Vega offers a JavaScript API.
For a quick overview of authenticated scanning using Vega, check out this video this video. If you’d like to get started, you can download Vega for free here.
6. Nmap (Free and Open Source)
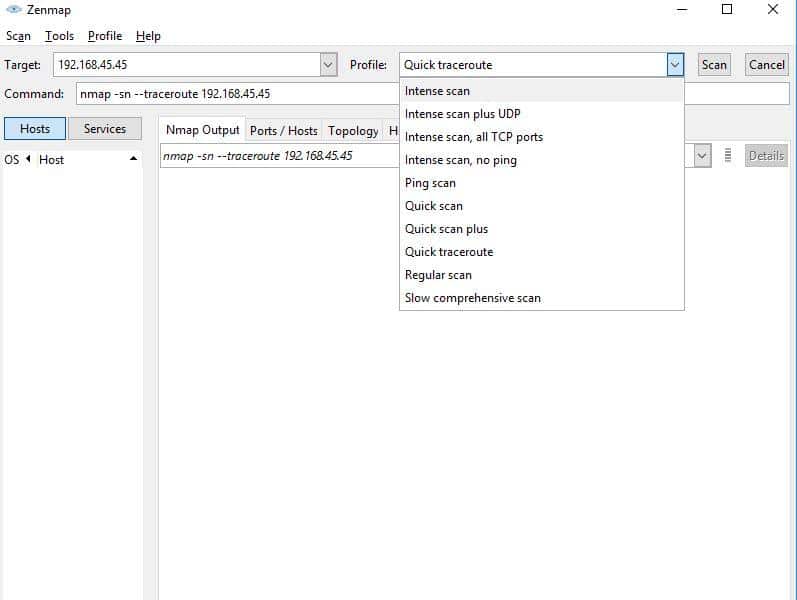
Nmap is a powerful CLI-based port scanning utility that many security professionals and penetration testers use regularly. Nmap offers a wide variety of switches and options that enable basic and advanced network scans and is often used as an integral part of other security applications. The specific feature of nmap that makes it a useful vulnerability scanner is the Network Scripting Engine (NSE). Nmap has a large community and active development team and this enables them to be able to quickly add vulnerability detection scripts as new vulnerabilities are revealed. For example, nmap developers released the “ssl-heartbleed” script within two days of Heartbleed’s announcement.
For a deeper dive on nmap, check out our Best Practice Ezine on the topic.
If you’re not comfortable with the CLI or just prefer a GUI, Zenmap is the official nmap GUI and helps you get the power of nmap within a graphical user interface.
Nmap is supported on Linux, Windows, Mac OS X, and a number of other operating systems. You can download the latest versions of nmap & Zenmap here.
7. ZAP (Free and open source)

ZAP (Zed Attack Proxy) is a free and open source security tool from OWASP. ZAP has a Java-based GUI (tip: be sure to download 32-bit or 64-bit Java depending on the version of Zap you have installed) as well as CLI options. In addition to supporting standard scans, ZAP supports a variety of plug-ins and features that extend its functionality. For example, ZAP supports Plug-n-Hack and has a Jenkins plugin for those looking to integrate ZAP as part of a continuous integration development environment.
You can download ZAP for free here.
Summary
That was our list of some of the top vulnerability scanners in 2018. Have you used any of these tools before? Do you think we left anything out? Let us know in the Comments section below.