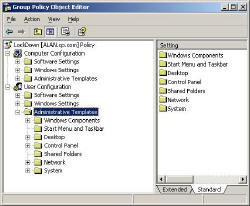
Group Policy – Administrative Templates
This section deals with the classic Microsoft Group Policies for Windows Server 2003. If you are new to Group Policies, this is the best place to start. Cut your teeth on these policies which are easy to understand, and fun to implement, for example, ‘Disable the Run Command’ or ‘Hide all icons on the desktop’.
While many administrators get fixated on policies which remove tabs, I find it satisfying to discover settings which improve users’ productivity, for example ‘Run Programs at Logon’. As I look through the hundreds of policies, I became aware that most of them would only be useful in specialist situations. What I have done is to highlight those policies that are worth implementing in a medium secure network.
Note: Microsoft created two sets of Administrative Templates, one for Users (this page) and one for Computers. The User Configuration folder has the richer set of policies.
Group Policy Topics
Administrative Templates
- Windows Components
- Start Menu and Taskbar
- Desktop
- Control Panel
- Shared Folders (little of interest)
- Network
- System
Pre-requisites before creating your User Group Polices:
- Access to a Windows Server 2003 domain controller. (Windows 2000 has different menus with fewer settings.)
- Install Group Policy Management Console (GPMC). If necessary get a copy from Microsoft’s site.
- Dedicate a test OU for your experimental policies. (Not essential, but safer than using the default domain policy)
- Create a Group Policy (GPO). right-click your policy, then edit.
- Navigate to the User Configuration (not Computer). Next expand the Administrative Templates.
‡
Guy Recommends: Permissions Analyzer – Free Active Directory Tool
I like thePermissions Monitor because it enables me to see quickly WHO has permissions to do WHAT. When you launch this tool it analyzes a users effective NTFS permissions for a specific file or folder, takes into account network share access, then displays the results in a nifty desktop dashboard!
Think of all the frustration that this free utility saves when you are troubleshooting authorization problems for users access to a resource. Give this permissions monitor a try – it’s free!
Download Permissions Analyser – Free Active Directory Tool
Windows 8 Group Policy Administrative Templates
Setting thus USB policies in the Administrative Templates will prevent people from reading (or writing) to a USB device, or copying files to the USB stick. Using a policy in the Computer Configuration section is simple and absolute. While configuring ‘Removable disks: Deny read access’ in the User Section is more flexible, it leaves you open to permissions problems, or to be realistic, opening the door for administrators to remove data from machines.
User Configuration
. Administrative Templates
… System
….. Removable Storage Access
……. Removable disks: Deny read access
(Enable)
Normally you would also Enable the ‘Deny execute access’, and ‘Deny write access’ next-door group policies. See more on Windows 8 Disable USB Group Policy
 Download my ‘Master Group Policies’ ebook only $6.25
Download my ‘Master Group Policies’ ebook only $6.25
The extra features you get in your eBook include: Spreadsheet with over 850 policies. Printer friendly version over Word A4 pages in Word.
See more User Group Policies for Windows
• Group Policy Overview • Group Policies • Control Policies • Desktop Policies
•Logon Script Group Policies • Administrative Template Policies •Group Policy Results
•Group Policy Management Console • Folder Redirection Windows Server 2003
If you like this page then please share it with your friends