Microsoft Windows 8 Event Viewer
The Windows 8 Event Viewer provides a marvellous interface to investigate critical and error messages in the logs.
You can examine not only the System and Application logs, but also Hardware Events and records of activity from IE and other programs.
Windows 8 – Event Viewer Topics
- Finding the Windows 8 Event Viewer
- New Features in the Windows 8 Event Viewer
- Strategies for the Window 8 Event Viewer
- Specific Tasks for New Event Viewer
- Windows 8 Security Event Log
♦
Finding the Windows 8 Event Viewer
I like to press Winkey +w, because this launches the Search box, and crucially, the focus is on Settings (rather than Apps).
Now type: "ev" you should see ‘View event logs’.
New Features in the Windows 8 Event Viewer
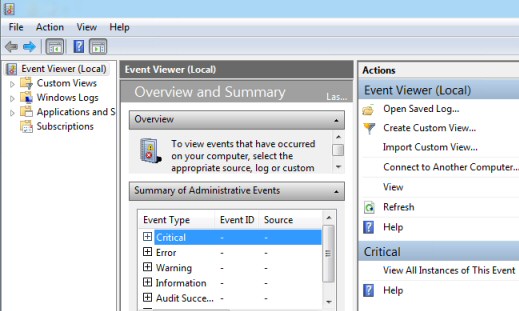
The biggest change Microsoft made to the Event Viewer came between XP and Vista with the introduction of the three pane interface. Windows 7, and now Windows 8 have merely refined the interface and extended the range of logs that you can interrogate.
Observe the 3 panes: Log List | Event Viewer | Actions
Strategies for the Window 8 Event Viewer
If you just want a quick ‘Health Check’ then start with the central ‘Overview and Summary’ pane, I suggest you work your way through the Critical messages followed by the Error messages. As the title indicates this is where you will find a list of important events collected from all the computer’s logs, the benefit is that you can work your way through the red dots quickly.
Alternatively, you could focus on the left pane and drill-down through a particular Windows log such as Windows Logs –> Application. If you want to view the logs on another computer than there is a link on the ‘Actions’ pane.
Additional Event Logs
In amongst the traditional Application, Security and System, are two extra logs, Setup and Forwarded Events. As you add new programs so the Setup log records events relating to the installation, which can be invaluable in troubleshooting what went wrong.
The ‘Forwarded Events’ log is used to collect events on other computers, you can specify the details via the Subscriptions menu. (See bottom left of above screenshot).
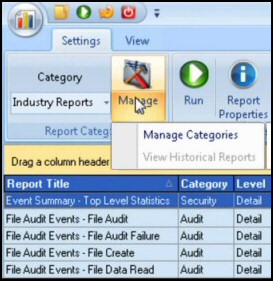
Guy Recommends: SolarWinds’ Log & Event Management Tool
LEM will alert you to problems such as when a key application on a particular server is unavailable. It can also detect when services have stopped, or if there is a network latency problem. Perhaps this log and event management tool’s most interesting ability is to take corrective action, for example by restarting services, or isolating the source of a maleware attack.
Yet perhaps the killer reason why people use LEM is for its compliance capability, with a little help from you, it will ensure that your organization complies with industry standards such as CISP or FERPA. LEM is a really smart application that can make correlations between data in different logs, then use its built-in logic to take corrective action, to restart services, or thwart potential security breaches – give LEM a whirl.
Download your FREE trial of SolarWinds Log & Event Management tool.
Application and Service Logs
®