How to Activate Windows 8’s Hidden Administrator Account
Terminology check: I am talking about an account that you don’t normally see in Windows 8 called ‘Administrator’.
As you may already know, you can create other accounts in the Control Panel which have administrative privileges, and are members of the Local Administrators group. However, while you can call such accounts Jo, Fred or even TechieAdmin, you cannot call them Administrator. The reason is that Administrator is already in the SAM database, you just need to turn it on.
I will show you how to activate ‘The Administrator’ account by typing a ‘Net User’ command. One pleasant side-effect of logging on with this super account is that you are not prompted for the annoying UAC dialog box.
Windows 8 Net User Administrator /Active:yes
- How to Enable the Windows 8 Administrator Account
- Local Group Policy Method to Enable the Administrator Account
- Benefits of Windows 8’s Hidden Administrator Account
- Check Windows 8’s User Accounts
- Summary of Windows 8 Administrator – Super User (Hidden Account)
♦
Instructions to Enable the Windows 8’s Administrator Account
Password Preparation: It’s not very helpful to activate the Administrator, but not to know the password!
Complex passwords can be a pain to remember, this is why I advise getting your characters ready in case the local group policy won’t allow a blank password, and is insistent on words with mixed case with numbers.
My password for this example: P$sw0rdY
Quick Instructions:
- Logon to Windows 8 using an account which is a member of the local Administrators group.
- As you launch the cmd prompt remember to select, ‘Run as administrator.’
- Net user administrator P$sw0rdY
- Net user administrator /active:yes
- Test the activated Administrator: Switch User, or logoff
- Logon as Administrator
Password P$sw0rdY (Hopefully your password is different!) - Once activated, you can also view the Administrator account in the Control Panel, Users Accounts.
Detailed Instructions to Activate the Windows 8 Administrator Account
- Logon to Windows 8 with another administrator’s username and password.

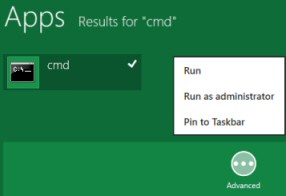
- At the Metro UI Type ‘CMD’
- When cmd appears right-click click ‘Advanced’, then select:
‘Run as administrator’ from the shortcut menu. - If you are not familiar with Net commands, start with:
Net help user - My idea is for you to learn more about the options for Net User. In particular, examine the syntax to set its password.
- Net user administrator P$sw0rdY
- Net user administrator /active:yes
- Check the message hopefully you get : ‘The command completed successfully.’
- Type plain: Net User. Compare with what you see in the Control Panel, User Accounts.
- Switch User, or logoff then, logon as Administrator Password P$sw0rdY (Your password should be different!)
Guy Recommends: A Free Trial of the Network Performance Monitor(NPM) v11.5
v11.5
SolarWinds’ Orion performance monitor will help you discover what’s happening on your network. This utility will also guide you through troubleshooting; the dashboard will indicate whether the root cause is a broken link, faulty equipment or resource overload.
What I like best is the way NPM suggests solutions to network problems. Its also has the ability to monitor the health of individual VMware virtual machines. If you are interested in troubleshooting, and creating network maps, then I recommend that you try NPM now.
Download a free trial of Solarwinds’ Network Performance Monitor
Troubleshooting Activate the Windows 8 Administrator Account
Trap 0 – Access Denied. The most likely reason is that you did not start the cmd prompt with elevated privileges. Try again; this time right-click and ‘Run as Administrator’.
Trap 1 – Spaces: There should be no space between the ‘/active’ and the colon(:).
/active :yes (Error: ‘You entered an invalid value for the /ACTIVE option.’)
/active:yes (‘The command completed successfully.’)
Trap 2 – Slash: You must remember the forward slash before the word /active
Net user administrator active:yes (Can give problems)
Net user administrator /active:yes (Always works)
I thank Rob Hilton for pointing out the above trap.
Trap 3 – The Word is ‘Active’: Pay close attention to the command name, it should be active, and not activate.
This technique also works on Windows 7 and Windows Server 2008, however, on the latter operating system it is more likely you want to desable the Administrator with:
Net user Administrator /active:no.
Recommended: Solarwinds’ Permissions Analyzer – Free Active Directory Tool
I like thePermissions Analyzer because it enables me to see WHO has permissions to do WHAT at a glance. When you launch this tool it analyzes a users effective NTFS permissions for a specific file or folder, and takes into account network share access, then displays the results in a nifty desktop dashboard!
Think of all the frustration that this free SolarWinds utility saves when you are troubleshooting authorization problems for user’s access to a resource. Give this permissions monitor a try – it’s free!
Download SolarWinds’ Free Permissions Analyser – Active Directory Tool
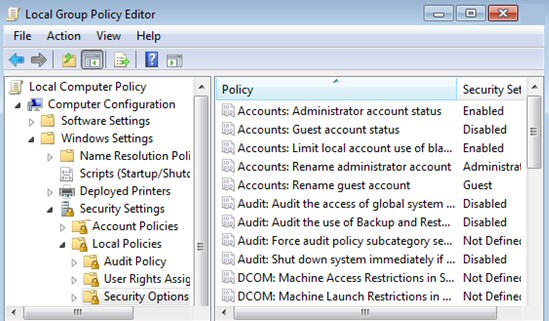
Local Group Policy: Windows 8 Administrator Account Status
Kindly sent in by Dave Waddell
If you prefer a simpler method to enable the Windows 8 Administrator account, explore the Local Security policy. Secpol.msc
- Launch the Windows Explorer. In the search box type: secpol.msc.
Trap: It won’t work unless you append the .msc extension. - Drill down to Local Policy, Security Options
- Double click Accounts: Administrator account status
- Select ‘Enable’. You have activated the account; almost certainly it has a blank password.
- Check Control Panel, User Accounts and Family Safety, User Accounts.
You can also see the resulting Windows 8 Administrator in the Control Panel, User Accounts folder see below.
Benefits of Windows 8’s Hidden Administrator Account
One benefit of Windows 8 Administrator account is that it has elevated privileges. Thus if you run CMD you don’t have to ‘Run as administrator’ before you get unrestricted access to the command line.
Another benefit of activating this Windows 8 Administrator account is that you don’t see the UAC dialog box when you make system changes. Although it is possible to suppress the UAC with a local group policy, there is a lingering fear that security is being weakened.
Another benefit of this hidden account as a ‘back door’, for example, if you are locked out of your main account. Sitting there now at your computer, you can’t believe that you will lock yourself out, yet logic dictates that somewhere in the world, someone has just done that: locked themselves out of Windows 8. Wouldn’t they love to know how to activate their administrator account?
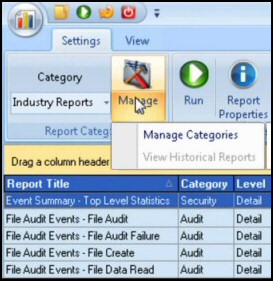
Guy Recommends: SolarWinds’ Log & Event Management Tool
LEM will alert you to problems such as when a key application on a particular server is unavailable. It can also detect when services have stopped, or if there is a network latency problem. Perhaps this log and event management tool’s most interesting ability is to take corrective action, for example by restarting services, or isolating the source of a maleware attack.
Yet perhaps the killer reason why people use LEM is for its compliance capability, with a little help from you, it will ensure that your organization complies with industry standards such as CISP or FERPA. LEM is a really smart application that can make correlations between data in different logs, then use its built-in logic to take corrective action, to restart services, or thwart potential security breaches – give LEM a whirl.
Download your FREE trial of SolarWinds Log & Event Management tool.
Check Windows 8’s User Accounts
Activating this super account provides a good opportunity to examine where you can configure Windows 8’s accounts. Click on the Start button, Control Panel and select –> User Accounts: My point is that you can check in the GUI which accounts have activated successfully. /Active:yes the account is visible. /active:no the User Name disappears from the list below.
Hidden Windows 8 Administrator’s SID
Every Windows account has a unique SID (Security Identifier). From NT 3.5 days it has been normal for THE Administrator’s account to have a SID ending in 500. I was surprised therefore, not to see any such SID number in Windows 8 – until I activated the hidden administrator. When I launched regedit and checked the HKEY_USERS, there was the famous SID: S-1-5-20-2354314321-13413-500, and it corresponded to The Administrator’s account.
One puzzle remained, in Windows 8 can you create, as opposed to activate, an account with a username of Administrator?
John Wolfe came up with the answer. ‘When I tried to name the original account as Administrator. I was told that the "Account already exists" ‘.
As usual, computer systems won’t allow two accounts with the same name.
See more about AutoAdminLogon »
Summary of Windows 8 Administrator – Hidden Account
One reason to activate the Windows 8 Administrator account is so that you are no longer nagged by the UAC (User Account Control) prompt. The procedure is straightforward, just launch a cmd prompt with elevated rights and type:
Net user administrator /active:yes.
The only trap is that many systems require a complex password so that you need to add a password to the command string thus
Net user administrator P$sw0rdY
Then
Net user administrator /active:yes
If you like this page then please share it with your friends
Microsoft Windows 8 Registry Topics
• Windows 8 Overview • Activate Windows 8 Administrator • Windows 8 Remove Shortcut Arrow
• Win 8 Registry Cleaner Review • Windows 7 Style Start Menu • Windows 8 Administrative Shares
• Win 8 Registry • Windows 8 Shortcut Desktop App • Windows 8 .Reg File • Windows 8 AutoRun