ADMT (Active Directory Migration Tool) and USMT (User Setting)Microsoft offer three utilities to assist with migrating to Windows Server 2003. Introduction
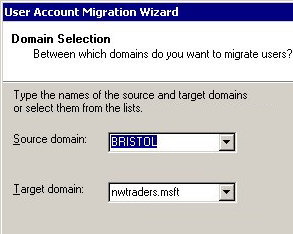
‡ ADMT v 2.0 (Active Directory Migration Tool)This is a great tool for copying user account information from one Windows domain to another Windows domain. I first used ADMT for transferring users in an NT 4.0 domain into a new domain in Windows 2003. These days ADMT is popular for migrating from Windows 2000 to Windows Server, particularly where you want to start with a brand new Active Directory forest. The prerequisite for using ADMT in Windows 2000 is that the domain has to be in Native mode. The crucial attribute is the sIDHistory, this enables the user object to be identified in the old and new domain. In addition to copying users, this utility also copies groups and even computer accounts. Conveniently, you can also copy the passwords. If you have scripting experience then you can use your skills to manipulate precisely what to migrate, ADMT provides a scripting interface. You will also need to create a trust so that the source (NT 4.0 or old domain) accounts trust the Windows 2003 domain. As a result the old accounts can be copied across to their new domain. Let me just clarify that the ADMT copies not moves the accounts, and that it is a one time move without any synchronization. Should you need account synchronization then deploy the ADC (Active Directory Connector). ▫ Obtain and Install Active Directory Migration ToolTo obtain the Active Directory Migration Tool dig out the Window Server 2003 cd and drill down to the \i386\ADMT sub-folder. Check the readme file and seek the .msi file. Alternatively, you can download all the files from Microsoft’s site, if you take this option, look out for ADMT v 3.0. ADMT is a well behaved program and the installation is straight forward. I am assuming that you have total administrative control of both domain, in particular you know the administrator passwords. If you use the actual administrator you can be sure that it is a member of groups such as Enterprise Admins and Schema admins. Those who struggle to differentiate between their right and left hands have trouble identifying which is their target and which is their source domain. Only you know the answer to these questions. One sneaky pre-requisite is that both source and target servers must have a C$ and Admin$ share. Guy Recommends: Permissions Analyzer – Free Active Directory Tool |