Introduction to Changing Registered OwnerThe purpose of this registry hack is to change the Registered to: as seen in the system icon. The scenario is that the wrong person has been assigned the registered owner. Perhaps the company had been merged or taken over. Our Task – to find and change the Registered OwnerWhen it comes to making changes to the registry, I favour Regedit over RegEdt32, because Regedit has a much better find, it also remembers the last place you visited. To me, RegEdt32 is clunky, and more difficult to use.  First Objective to get to the CurrentVersion registry hive. First Objective to get to the CurrentVersion registry hive.
Method Use the Find (menu) in Regedit, but be prepared to use F3 if you do not get to the RegisteredOwner at first. Note RegisteredOwner is all one word with no spaces. Alternative Method: Drill down to: HKLM\Software\Microsoft\WindowsNT\CurrentVersion\RegisteredOwner Note the path at the bottom of the diagram. Second Objective change RegisteredOwnerDouble Click RegisteredOwner then change the value to what you want. Re-open the System Icon and check your new value Bonus Objective change RegisteredOrganizationJust above the RegisteredOwner, you will see a REG_SZ RegisteredOrganization, why not change this as well to reflect your preference.  Guy Recommends: The Free Config Generator Guy Recommends: The Free Config Generator
SolarWinds’ Config Generator is a free tool, which puts you in charge of controlling changes to network routers and other SNMP devices. Boost your network performance by activating network device features you’ve already paid for. Guy says that for newbies the biggest benefit of this free tool is that it will provide the impetus for you to learn more about configuring the SNMP service with its ‘Traps’ and ‘Communities’. Try Config Generator now – it’s free! Download your free copy of Config Generator - Use Regedit rather than Regedt32 because it has a wonderful FIND
- Use the REGISTRY Export setting as a precaution
- Rename settings you do not needed or want, avoid deleting anything in the registry
- If you are following advice, check whether it says ADD or Change. With ADD you need an extra step.
- Practice remote registry editing to prepare for an emergency
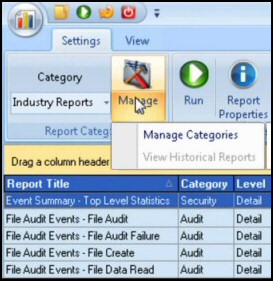
Guy Recommends: SolarWinds’ Log & Event Management Tool LEM will alert you to problems such as when a key application on a particular server is unavailable. It can also detect when services have stopped, or if there is a network latency problem. Perhaps this log and event management tool’s most interesting ability is to take corrective action, for example by restarting services, or isolating the source of a maleware attack. Yet perhaps the killer reason why people use LEM is for its compliance capability, with a little help from you, it will ensure that your organization complies with industry standards such as CISP or FERPA. LEM is a really smart application that can make correlations between data in different logs, then use its built-in logic to take corrective action, to restart services, or thwart potential security breaches – give LEM a whirl. Download your FREE trial of SolarWinds Log & Event Management tool.
If you like this page then please share it with your friends
Windows Vista Registry Tweaks: |