Longhorn Registry Hack – ConsentPromptBehavior
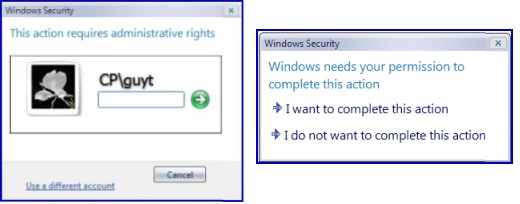
You can modify Longhorn’s new User Account Protection Behavior with ConsentPromptBehavior. It is a case of the more security you have the more work there is for you. Windows Longhorn (and Vista) protects the administrator from the excessive power and privileges of their own account. However, when ever the administrator needs elevated rights, Longhorn provides a dialog box where the user types their password. What my registry hack does is replace the need to type a password by merely clicking on ‘ I want to complete this action’. In some ways ConsentPromptBehavior reminds me of AutoAdminLogon.
How to alter User Account Protection Behavior
Well I knew I was on familiar ground when I spotted my first registry hack for Longhorn: ConsentPromptBehavior. The scenario is that you are logged on as administrator and then need elevated rights to configure a setting, for example, install a driver.
Technically, when you want to perform an administrative action in Longhorn, the operating system switches tokens and asks you to type in your administrator password – boring. Boring because most likely, the password consists of at least 8 characters and probably includes a non-alphanumeric squiggle or two, moreover, you get frustrated because you changed it yesterday and now cannot remember precisely which characters you chose.
The advantage of ConsentPromptBehavior is that it allows you to just click on a button which says ‘I want to complete this action’. No more struggling with the pound, ampersand or what ever strange keystrokes your password requires.
Does ConsentPromptBehavior compromise the whole idea of extra security? Yes and No. Yes, if you leave your machine unlocked and some psycho takes advantage of an unattended machine. No because it still protects you from rogue programs such as maleware that are trying sneaky back door activities on your machine. If you are concerned about security then do not make this change. If security is not paramount, and you know who you where your real security enemies are, then go ahead, join me by adding ConsentPromptBehavior to the registry.
Here is the registry key for ConsentPromptBehavior:
HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System
"ConsentPromptBehavior" =dword:00000001
Remember to logoff, then logon before trying to exercise an administrative right.
Original behaviour: enter password. After setting ConsentPromptBehavior=1, just click on ‘ I want..action’
 Guy Recommends: The Free Config Generator
Guy Recommends: The Free Config Generator
SolarWinds’ Config Generator is a free tool, which puts you in charge of controlling changes to network routers and other SNMP devices. Boost your network performance by activating network device features you’ve already paid for.
Guy says that for newbies the biggest benefit of this free tool is that it will provide the impetus for you to learn more about configuring the SNMP service with its ‘Traps’ and ‘Communities’. Try Config Generator now – it’s free!
Download your free copy of Config Generator
Registry Learning Points
Trap: Beware, at first I overlooked the \System sub folder. The first experiment failed, but then when I looked in the System folder, I knew I was on the right track because ConsentPromptBehavior already existed, and all I had to do was change its value from 2 –> 1
Familiar Ground Story
When I found this ConsentPromptBehavior registry hack in Longhorn, I felt on familiar ground. Registry Hacks are often an indulgence, at least that is my justification for digressing with this story.
Mr Stanley saw a man on the shores of Lake Tanganyika and famously said: "Dr Livingstone, I presume?". The irreverent version has it that Mr Stanley sneaked up to a strange tent and heard voices. At first Mr Stanley thought they were hostile natives until he heard Dr Livingstone say; ‘You swine, you just trumped my *** Ace’, at which point he knew he was back amongst Gentlemen.
Monitor Your Network with the Real-time Traffic Analyzer
The main reason to monitor your network is to check that your all your servers are available. If there is a network problem you want an interface to show the scope of the problem at a glance.
Even when all servers and routers are available, sooner or later you will be curious to know who, or what, is hogging your precious network’s bandwidth. A GUI showing the top 10 users makes interesting reading.
Another reason to monitor network traffic is to learn more about your server’s response times and the use of resources. To take the pain out of capturing frames and analysing the raw data, Guy recommends that you download a copy of the SolarWindsfree Real-time NetFlow Analyzer.
Summary
When you edit this registry key, you change the behavior of the User Account Protection menu. Specifically Longhorn provides a simpler menu where you can simply click on a confirm action menu. For security reasons, the normal behaviour is to require a password, and if your domain enforces complex passwords, this can be frustrating and time consuming.
More Registry Tweaks:
• Registry Hacks • Registry Hacks Getting Started • Registry Secure Hacks
• Registry Hacks Low Disk Space • Registry Hacks Autorun • Registry ConsentPromptBehavior
• Registry Hacks Cached Logons • Registry Hacks ContextMenuHandlers • God Mode