Evaluate SolarWinds' LEM (Log & Event Manager 6.2)
There are three aspects to LEM:
a) Keeping your network running smoothly.
b) Computer security.
c) Compliance to industry standards.
As we'll see, both the management and the resultant corrective actions rely on LEM’s clever analysis of logs that already exist on your servers and routers.
SolarWinds LEM Evaluation
- Three Benefits of Log & Event Management
- Video Explaining Log & Event Manager
- How Does Log & Event Management Work?
- Security Information & Event Management (SIEM)
- See also Event Log Forwarder for Windows
Three Benefits of Log & Event Management
The most difficult task of my review is to convey the power of processing data, yet at the same time, explain the simplicity of operating the GUI. Regarding the logs, LEM doesn’t re-invent the mib structure of SNMP, or the flow control of syslog, it simply reads existing logs on your server and router. Working with the correlation rule builder is straightforward, but only because programmers have created hundreds of routines, which work away in the background analyzing the logs.
a) Identifying Pure Server and Network Problems
Wearing your operations manager hat, LEM will alert you to problems such as when a key application on a particular server is unavailable. It can also detect when services have stopped, or if there is a network latency problem. Perhaps LEM’s most interesting ability is to take corrective action by restarting services, or isolating the source of unauthorized network traffic.
You can configure Log & Event Management so that you (or other key personnel) can receive instant alerts if important events occur, meanwhile, LEM’s correlation rule builder could have been programmed to take corrective action in real-time. Once you have the problem under control, you can track the history in the logs and thus find the event that caused the glitch. It’s also worthwhile adjusting, or creating new rules to improve the response if such events were to occur again.
b) Enforcing Security Through Log & Event Management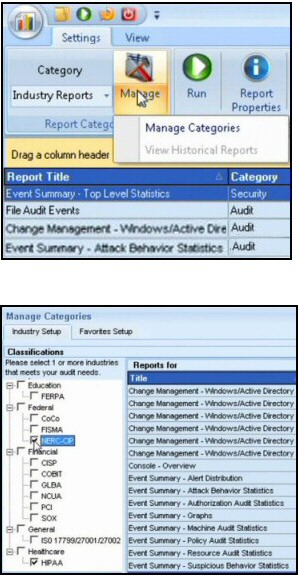
Being a ‘country boy’, I have never had security drilled into me; consequently, I am grateful for the way the event manager gives me an alert if there is a security breach because I had not locked down permissions or user rights. I also took the opportunity to understand how LEM can employ settings to restrict the usage of USB devices.
Moving on to malware, what I find is that even if I keep my anti-virus definitions up-to-date, sooner or later a new virus seems to emerge from no-where. It’s great to have the peace of mind that not only will LEM alert me if there is an attack, but also I can also use LEM’s correlation rule builder to take counter-measures against typical actions of viruses, and best of all I can isolate the source and thus stop the virus spreading on the network.
c) Compliance with Industry Standards
One thing I have noticed about SolarWinds in this appraisal is their supply of templates. They encourage dedicated geeks, who spend hours creating clever settings, to making them available to the rest of the ‘Thwack’ community.
In the case of LEM, Thwack has collected 300 out-of-the box templates to cater for any compliance test you I could imagine. A simple example is Authentication – who is logging on where and when.
In my role as server consultant company managers often ask me how they would know if there was a rogue techie in their IT department? I say just ask your top IT geek for the change management log. I tell managers you don’t have to understand it, or even read it, but just asking for the log sends the message that you may just spot any security breach, or you might call in not me, but a dedicated security consultant who would find it!
LEM encourages managers to improve on my advice by setting up compliance reports themselves, and publishing at least some of results so that everyone in the organization knows the standards expected. Download your free trial of the SolarWinds Log & Event Manager.
Video Explaining Log & Event Manager
by Rob Johnson, Geek at SolarWinds
Here is an interesting way to review SolarWinds' LEM software:
How Does Log & Event Management Work?
The key point is all the data is already out there on your network. All you need is for the log event manager to deploy agents, which collect syslog information from routers, read anti-virus programs, and trawl the operating system’s numerous logs. LEM’s skill lies in using hundreds of rules to analyze all this data in real-time. Its mission is to correlate events, for example abnormal traffic at a router is related to errors in a log at the server. As for the rules, you can rely on the built-in logic, or better still, amend the defaults and thus develop tailored responses to actual situations on your network.
More than just analyzing and presenting data, LEM is empowered to take corrective action; for instance, it can restart services, or isolate machines affected with viruses. I also like the way you can set rules to disable USB ports if an unauthorized user tries to copy data to a memory stick.
However, I think that the killer reason why people will trial, then buy LEM, is for its compliance capability. It’s not just financial companies that need to abide by industry rules, most companies need to comply with a standard such as CISP or FERPA. If, like me, you find this security fulfilment a drudge, then you will breathe a sigh of relief to have LEM take care of business, to check the logs, compare with criteria, then provide a detailed compliance report.
Hidden Benefits of Log & Event Management
LEM will assist an organization by boosting morale, and supporting its work ethos. Firstly, it will exude a sense security by protecting the users from viruses; it is also protective in a mothering way by taking action when things go wrong, such as alerting a supervisor who can help someone who has accidentally locked-out their account.
To my way of thinking, by doing the analysis with a thoroughness that only automation can achieve, LEM frees you to tackle the interesting part, setting the criteria for alerts, and my favourite, configuring actions based on events. For example, through analysis of the logs LEM can detect which application users are launching. Then you can configure actions to block their games of poker, ‘Civilization’ or ‘World of Warcraft’. It’s up to you set the tone and force of the corresponding message which tells the user to stop playing and get back to work! But it’s not all being Mr Nasty, you can also be Mr Nice and help them if they are locked out, or restart their legitimate apps automatically if they hang. See also Alert Central review.
An Easy Installation is More Important Than You Think
The litmus test for my evaluation of the Log & Event Management app is will it install effortlessly? It is my belief that all programs should be as easy to install as Microsoft Office – and LEM passes this test with flying colours. I am obsessed with smooth setups because, if a program installs easily, then it’s my experience that it will be stable and behave predictably.
Guy says that all software instillations should be intuitive. In the case of LEM, it’s testament to the care of the SolarWinds engineers and programmers that you can install LEM, and get it running, without any knowledge of SQL databases or Crystal reports. And the only knowledge of VMware you need is that you have got a licensed copy! OK, you must also have 8GB of RAM and 2 processors. The reason that beginners find it easy to get LEM up and running is because Wizards will guide them through the menus.
Improvements in Log & Event Manager 6.2
- Threat Intelligence with feeds of statistics and trends
- Automatic Connector Updates
- Appliance Details now displayed on the Settings Page
- Vulnerabilities patched
- 11 Configuration Items addressed
Setting up the LEM application is as easy as 1, 2, 3.
- Step 1 Download the LEM gadget Zip, extract the single executable.
- Step 2 Deploy the OVA file into in your VMware virtual machine.
- Step 3 Install desktop software in the VM.
(While I have omitted the detail, my point is you don’t need itemised instructions, just follow the wizard.)
Getting Started Once LEM is Installed
- Explore the SolarWinds Log & Event Manager console, check the tabs.
- Visit OPS CENTER.
- Play with the simulation data.
For More Information on Installing LEM, Review this SolarWinds Video:
Remember:
Download your free trial of the SolarWinds Log Manager gadget.
Computer and Network Performance
In addition to providing the Log & Event Manager, SolarWinds have an Orion suite of applications, most notably the Network Performance Monitor (NPM). The difference between these two apps is that LEM is concerned with monitoring the logs, then providing alerts and corrective action. Whereas NPM provides a dashboard with readings for factors such as CPU load (say 25%), capacity utilization (e.g. 67%) or network latency (350ms). It’s often only by comparing two tools that you get true understanding of what each can achieve, evaluate the Network Performance Monitor (NPM).
Summary: Review of SolarWinds Log & Event Management
There are three important tasks that LEM can help you achieve, IT compliance, computer security, and network management. Providing you already have VMware installed LEM is straightforward thanks to the point and click wizards.
Once LEM is up and running take the time to check the library of filters which correlate the data recorded in your various logs. Finally, combine business with pleasure and configure automatic outcomes for a given combination of events as reported by the logs.
Free and 30-day Trial Virtual Machine Software
Here are my recommendations for additional handy utilities. Many of these downloads are free, while others are fully-functional, but time limited. SolarWinds are happy to provide you with a free specialist tool, which is ideal for testing, and then supply a more comprehensive suite for larger organizations. To let you into a secret, for small networks, the free tool is all you’ll ever need.
• Virtualization Manager • SolarWinds Application Monitor • Storage Response Time Manager
• VM Monitor • User Device Tracker • Free Network Bandwidth Monitor • Free SNMP Tool
• VM-to-Cloud • SolarWinds WMI Monitor • LanSurveyor • SolarWinds SIEM • Home



