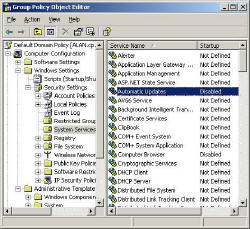
Security Settings – System Services
Something different. Policies that affect the operating system rather than the users. If you are familiar with the Services snap-in, then you may already have ideas about which services should be disabled, for instance Telnet, and FTP.
Security is our watchword in this section, so let us disable services that will never be needed, especially if they could be used by hackers.
* Guy’s candidates for services to disable
- FTP
- Trivial FTP
- Telnet
- Computer Browser
- WWW Publishing
‡
Services where you need to decide
- Error Reporting Service
- Automatic Updates
- Remote (Various)
- PowerShell Services
 Configuration
Configuration
Take the time to go through the list and decide which services to disable with a policy. In terms of strategy, I advise creating a Group Policy or eve an OU for each type of machine, for example a server OU where you disable services such as IIS.
Once the machine starts, you can over-ride the policy, simply go to the Services, double click the particular services and select one of these start-up options:
- Automatic
- Manual
- Disabled.
Monitor Your Network with the Real-time Traffic Analyzer
The main reason to monitor your network is to check that your all your servers are available. If there is a network problem you want an interface to show the scope of the problem at a glance.
Even when all servers and routers are available, sooner or later you will be curious to know who, or what, is hogging your precious network’s bandwidth. A GUI showing the top 10 users makes interesting reading.
Another reason to monitor network traffic is to learn more about your server’s response times and the use of resources. To take the pain out of capturing frames and analysing the raw data, Guy recommends that you download a copy of the SolarWindsfree Real-time NetFlow Analyzer.
Finally…
A final thought, rather than being negative all the time, why not seek out services that you positively wish to set to Automatic Startup? ‘Special Administration Console Helper’ springs to mind.
�
Next: Administrative Templates
 Download my ‘Master Group Policies’ ebook only $6.25
Download my ‘Master Group Policies’ ebook only $6.25
The extra features you get in your eBook include: Spreadsheet with over 850 policies. Printer friendly version over Word A4 pages in Word.
See more security Group Policies
• Group Policies •Troubleshooting Group Policies • Group Policy Tactics
•Group Policy Security • Audit Logon Events •Security Event Log •Security Options
• Security System Services • Security System •Security User Rights •Security Software
If you like this page then please share it with your friends