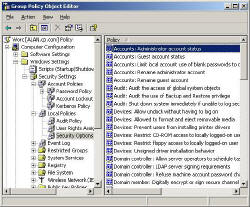
Local Polices – Security Options
Security Options is an apt heading. Lots of protection and certainly zillions of choices. Working your way through these policies will help to clarify what level of security you need, low, medium or high.
Remember that the more security that you implement, the more work there will be for the administrator. Therefore, I would resist high security settings unless your directors demand the highest protection.
Audit Policy
User Rights
Security Options.
* Guy’s Top Three Security Options
‡
Administrator’s Account
Probably the most important security question is: ‘What are you going to about the Administrator account?’ The problem is that this built-in account is a liability because hackers know that: If it’s a Windows operating system, then there will always be an Administrator account to hack. The answer is to * ‘Rename Administrator Account’, and possibly to disable the ‘Administrator Account Status’. Naturally, create a new administrator, but choose a name that blends in with the other user accounts.
![]() (Double) check that double negatives do not obscure your objective for the administrator’s account.
(Double) check that double negatives do not obscure your objective for the administrator’s account.
Other Security Options are neatly categorised thus:
Devices
You really should come to a decision about unsigned device drivers, my guess is that as time goes on, it will be more important to allow only signed, approved, certified drivers.
Domain Controller
Trust me, there is nothing for ordinary mortals here. Specialist policies only.
Interactive (Keyboard) Logon
The policy * ‘Do not display last user name‘, causes emotions to run high. The two sides of the argument are:
1) That on communal machines one user can inadvertently lockout another user’s account. What they do is keep their head down and not see that someone else’s name is in the logon box, as a result they accidentally type in their password for the other person’s account. The result is a colleague’s account is unfairly locked out. So enabling ‘Do not display last user name’, will prevent that particular user error.
2) On the other hand, enabling ‘Do not display last user name’ for machines where the same user always logs on, only causes frustration and resentment. This is because it’s really unnecessary for anyone to type in their username at every logon if no-one else ever sits at that computer.
A prediction, one day we will all use smart card logons, the only debate is what form they will take, finger print, credit type cards or retina scan (yuk). So, my advice is to put Require Smart Card Logon on your ‘To Do’ list.
Monitor Your Network with the Real-time Traffic Analyzer
The main reason to monitor your network is to check that your all your servers are available. If there is a network problem you want an interface to show the scope of the problem at a glance.
Even when all servers and routers are available, sooner or later you will be curious to know who, or what, is hogging your precious network’s bandwidth. A GUI showing the top 10 users makes interesting reading.
Another reason to monitor network traffic is to learn more about your server’s response times and the use of resources. To take the pain out of capturing frames and analysing the raw data, Guy recommends that you download a copy of the SolarWindsfree Real-time NetFlow Analyzer.
Microsoft Network
By now you will have come to a decision on whether you are a high, medium or low security company. Only high security organizations will need these specialist settings for certificates.
Network Access for client and server
Useful settings here, policies which will assist you in keeping out the bad guys without affecting the good guys. For example, if you disable remote registry editing who will that affect? Only the bad guys.
Kiwi Syslog Server 
Free Utility to Analyze Your Network Messages
Syslog messages contain useful information for troubleshooting network problems. When something goes wrong then surely there will be an error message in the syslog datagram – if only we can find that record and interpret the event.
Here is a utility to capture and analyze network messages. The Kiwi Syslog Server filters messages and creates advanced alerts. View your syslog data via web access.
Download your free download of Kiwi Syslog Server
Recovery Console
Just two settings. Control the Shut Down without logon button, and decide on clearing pagefile on shutdown. The later will mean it takes slightly longer to reboot, but the system will be more secure.
System
Frankly, another specialist section which you would only need to visit rarely. Make that extremely rarely!
Summary of Group Policy Security Options
Keep in mind that the more security settings you implement, the more work there will be for the administrator. The most interesting policy in this section is: ‘Do not display last user name’.
Next: Event Log
 Download my ‘Master Group Policies’ ebook only $6.25
Download my ‘Master Group Policies’ ebook only $6.25
The extra features you get in your eBook include: Spreadsheet with over 850 policies. Printer friendly version over Word A4 pages in Word.
See more security Group Policies
• Group Policies •Troubleshooting Group Policies • Group Policy Tactics
•Group Policy Security • Audit Logon Events •Security Event Log •Security Options
• Security System Services • Security System •Security User Rights •Security Software
If you like this page then please share it with your friends