Group Policy Audit Policy
This is what a good audit policy will discover:
- Who is trying to logon.
- Which files have been deleted.
- Who did it!
Incidentally, unlike other Group Policy settings, Microsoft has not created an ‘Explain’ tab for these policies, however, if you right-click and select ‘Help’, there is a comprehensive explanation of each policy setting.
Trap: If you are intending to set Local Policies for your actual Windows Server 2003 Domain Controller, then you should go to the All Programs, Administrative Tools, Domain CONTROLLER policy. (Audit policies for Member Servers and XP clients can be set at the Domain or OU level).
Microsoft Audit Logon Events Topics
User Configuration
Windows Settings
Local Policies
Audit Policy
- Logon Events
- Object Access – Master Switch.
- Three administrator security settings
- Process tracking – a disciplinary offence?
‡
* Guy’s Top Two Audit Policies
Group Policy for Logon Events
Watch out for two similar and potentially confusing policies, ‘Audit Account Logon events’ and ‘Audit Logon events‘. The difference is that Audit Logon events (the shorter one) means that you are checking who is pressing Ctrl Alt, Del at the domain controller (or desktop); whereas the Audit Account Logon events (the longer one) generates an event every time a user connects to that server across the network.
In terms of strategy, decide whether you simply want to record logon failures – possible illegal access attempts, or whether you also need to audit success.
Once you enable security policies, check Microsoft’s Event Viewer’s Security Log (not system log) for user activity. Another tip: once you become serious about security, increase the size of the log from 512 K to at least 10 Mb.
Object Access – The ‘Master Switch’ for file and print Auditing
If you need to record who is accessing shares, or who is deleting files, then first you must enable, * ‘Audit Object Access’. Only when you have thrown the Object Access ‘master switch’, can you start checking who is doing what to your folders and printers.
Three administrator security settings to consider
I have lumped together, account management, privilege use and directory service access. These are three settings that only big companies need to audit. It is all well and good recording lots of events, but ask yourself, ‘Who will have the time to scour through zillions of events?’ Better to record only essential settings, that way, you will easily spot security breaches.
Process tracking – A disciplinary offence?
If you enable process tracking you should get the sack! Stern words to make a serious point. My point is that Auditing eats up CPU cycles, in fact, process tracking is so intensive that your server will grind to a halt. Perhaps you can see why I would forbid process tracking. People then ask me ‘Why would Microsoft include process tracking if it’s so crippling?’. The answer is so that developers can troubleshoot their new programs.
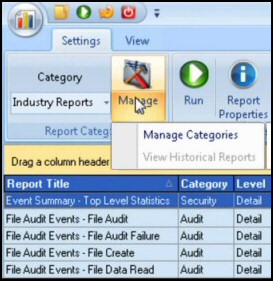
Guy Recommends: SolarWinds’ Log & Event Management Tool
LEM will alert you to problems such as when a key application on a particular server is unavailable. It can also detect when services have stopped, or if there is a network latency problem. Perhaps this log and event management tool’s most interesting ability is to take corrective action, for example by restarting services, or isolating the source of a maleware attack.
Yet perhaps the killer reason why people use LEM is for its compliance capability, with a little help from you, it will ensure that your organization complies with industry standards such as CISP or FERPA. LEM is a really smart application that can make correlations between data in different logs, then use its built-in logic to take corrective action, to restart services, or thwart potential security breaches – give LEM a whirl.
Download your FREE trial of SolarWinds Log & Event Management tool.
Examples of Auditing Logon Events
Note: The following account logon events are recorded in the event logs on domain controllers for domain account activity, but on local computers for local account attempts.
528 A user successfully logged on to a computer. (Will also record a logon type, for instance, 2= Interactive, 3=Network.
529 Logon failure. A logon attempt was made with an unknown user name or a known user name with a bad password.
Summary for Group Policy -> Security Settings -> Local Polices -> Audit Policy
Here we have the classic Group Policies to track who does what on the servers or local computers. Some audit settings need to be all the time, while other you need just for troubleshooting. Configuring the Group Policy settings is not difficult, provided you have an action plan based on the appropriate security classification of your organization.
 Download my ‘Master Group Policies’ ebook only $6.25
Download my ‘Master Group Policies’ ebook only $6.25
The extra features you get in your eBook include: Spreadsheet with over 850 policies. Printer friendly version over Word A4 pages in Word.
See more security Group Policies
• Group Policies •Troubleshooting Group Policies • Group Policy Tactics
•Group Policy Security • Audit Logon Events •Security Event Log •Security Options
• Security System Services • Security System •Security User Rights •Security Software
If you like this page then please share it with your friends