Introduction to Terminal Services Configuration
Terminal Services is Microsoft’s thin client. The remote desktop protocol gives an XP Professional experience to users, who for a variety of reasons, cannot use a real XP desktop. Even if you have no intention of deploying Terminal Services for users, it is well worth checking the Windows Server 2003 settings so that you can take advantage of the two free administrative connections.
Terminal Services has its own RDP (Remote Desktop Protocol). Most of the user’s settings are configured at the Terminal Services Configuration snap-in, through the 8 tabs underneath under the RDP settings.
In terms of overall Remote Desktop strategy, there are three places to check, here at the RDP-Tcp properties on the server, at the client Options button, and through Group Policy. (Typical Microsoft to provide 3 ways of Configuring Terminal Services.)
8 Settings for RDP-Tcp
To start with, I assume that you are logged on at the Windows Server 2003 console. From the Administrative Tools, launch the Terminal Services Configuration interface. (Beware, there are 3 Terminal Services Snap-ins.)
Now you should see the 8 tabs, which you see under the Connections folder of the RDP-Tcp icon.
‡
General
Microsoft has not left much to configure on the general tab. The only configuration you need is if you have installed certificates or a third party logon / authentication package for the XP client.
Logon Settings
Again, in most instances, Microsoft’s defaults will suffice. The one exception is testing, when I am testing new Group Policies it is annoying to have to keep entering the password, so under these circumstances, I disable the prompt for a password. A real-life application could be if you only use Terminal Services as a Kiosk / internet cafe.
Sessions
The sessions tab is useful for setting timeouts. I like to control what happens if a Remote Desktop user is idle for hours on end. There are two potential problems, firstly that idle user could be hogging a Terminal Service license, which someone else could use. Secondly, if you have dozens of idle users then the Windows 2003 server’s performance would degrade slightly because it still has to allocate resources to those sessions.
See Windows 8 Remote Desktop Connection.
Environment
Most of the time the defaults will suffice, however, if necessary you could start a special program for each session. I know that one company that created special shells and messages, but equally, I know that many users found them annoying because they were not relevant to how they used Remote Desktop.
Guy Recommends: A Free Trial of the Network Performance Monitor (NPM) v12
v12
SolarWinds’ Network Performance Monitor will help you discover what’s happening on your network. This utility will also guide you through troubleshooting; the dashboard will indicate whether the root cause is a broken link, faulty equipment or resource overload.
Perhaps the NPM’s best feature is the way it suggests solutions to network problems. Its second best feature is the ability to monitor the health of individual VMware virtual machines. If you are interested in troubleshooting, and creating network maps, then I recommend that you give this Network Performance Monitor a try.
Download your free trial of SolarWinds Network Performance Monitor.
Remote Control
Here is where you can have fun. The best configuration is to setup remote control whereby the users allow administrators to interact. In fact, the most fun is where you not only view the session but interact with the desktop whether or not the user invites you. I am duty bound to point out that administrators should act responsibly and not abuse their privileges and rights. Managers reading these notes should ask for a detailed report on remote control, because even in view mode, techies could see what the financial manager or other sensitive staff were doing.
On a more general point, managers should always remember that techies are all powerful and could read their email and see or their files. Even with certificates and encryption, if I was an employee, I would always believe that the network manager could see everything that was happening on the network. That pre-supposes that the network manager had the time and found my email and files worth the effort of looking at!
To drive my point home, most security breaches are internal rogues not external hackers.
Client Settings
Definitely a tab to check. Here is where you control local resources. It is all too easy to forget that with Terminal Services it is as thought the user is logged on at the actual server. To digress, the classic ‘gotcha’ is where the users shutdown the server when they think they are shutting down their own XP machines. Naturally you control shutdown via Group Policies.
Meanwhile, back with the Client Settings tab, these menus move resources like the printer from the server to the true local client machine.
Network Adapter
Incidentally, here is where you can tell whether Terminal Services has been installed, or whether the server is just in the default Remote Administration mode. The key setting is the Maximum number of connections, in Remote Desktop mode Microsoft will only allow 2 connections, whereas the full Terminal Services configuration permits unlimited connections. One reason that you may wish to reduce this number is the performance of the server, the other would be the number of licenses.
Permissions
The main reason for looking at the classic permissions tab is to remind yourself that there is such a built-in group as Remote Desktop Users. Microsoft’s best practice suggests that you use this Remote Desktop Users to decide who has the privilege of using Terminal Services.
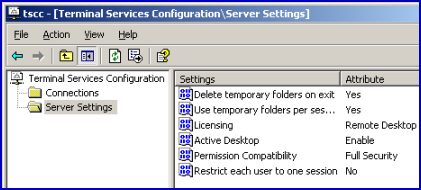
Server Settings
The server Settings folder keep a record of choices that you made when you installed Terminal Services, the interface makes it easy to go back and adjust a particular attribute.
The diagram on the right was taken from a session where I changed the ‘ Restrict each user to one session ‘ from No to Yes.
Terminal Services Summary
Even though configuring Microsoft’s Terminal Services is easy, there are still 8 tabs that you should know inside out. Particularly when troubleshooting, you need to be able to find remote control settings or session timeouts.
If you like this page then please share it with your friends