Introduction I Have Updated This Section – Here Are the Links:
- New Registry Section For Windows 7.
- Registry Section for Vista, but also works with XP.
- PowerShell Registry Editing
♦
My aim in this section is to give you experience, confidence and satisfaction of making changes to the Windows registry.
There are times when you read about a Windows Server 2003 feature but there is no icon to implement it. So the only way to test the item is to change a setting in the registry. Another reason to master registry editing is so that you can remotely troubleshoot a machine via Regedit.
The executables to hack the registry are Regedit (or Regedt32). The newer versions of Regedit remember the last place you visited which is extremely useful. If you have not been to the registry before, go to the START (Button), Run, regedit, OK.
How Dangerous is Editing the Registry?
People give dire warnings about changing the registry. My view is that changing settings via the registry is no more hazardous than say – configuring the monitor refresh rate through the Control Panel. You may hear that if you make a mistake you can cripple your system; I find that if you type in the wrong key value nothing happens! However I once saw a ‘gung-ho’ individual delete a whole section of the registry. This would have been disastrous if I had not exported the relevant section, so we just imported it and solved the problem.
 Guy Recommends: The Free Config Generator
Guy Recommends: The Free Config Generator
SolarWinds’ Config Generator is a free tool, which puts you in charge of controlling changes to network routers and other SNMP devices. Boost your network performance by activating network device features you’ve already paid for.
Guy says that for newbies the biggest benefit of this free tool is that it will provide the impetus for you to learn more about configuring the SNMP service with its ‘Traps’ and ‘Communities’. Try Config Generator now – it’s free!
Download your free copy of Config Generator
Registry Tips
- Use Regedit rather than Regedt32 because it has a wonderful FIND.
- Use the REGISTRY Export as a precaution before you experiment.
- Rename settings you do not needed or want, avoid deleting anything in the registry.
- If you are following advice, check whether it says ADD or Change. With ADD you need an extra step.
- Practice remote registry editing to prepare for an emergency.
Best Practice for Editing the Vista Registry
- Before you make any changes to the registry settings, get into the habit of exporting at the branch of the registry that you are working with.
- Backup the system state before you try anything radical in the registry.
- Check out the .sav files in the \system32\config folder.
- Research Volume Shadow Copy, and test how it restores a previous version of your registry files.
- If your computer has a serious problem, which requires pressing F8 at boot-up, remember to try Last Known Good as your first recovery option.
- Seek alternative methods; think laterally. Instead of risking making changes with your registry editor, what else could you do? I urge you to consider configuring a Group Policy rather than tweaking the registry. Occasionally Vista may provide a new GUI to configure a setting, for example, instead of launching regedit and changing the value for AutoAdminLogon, you could launch the Control Panel –> Users and un-tick the setting called, ‘Users must enter a user name and password.’
- Learn how to perform a remote registry edit with: Connect Network Registry.
- As you work through my registry examples, make a point of studying each page’s ‘Key Learning Points’.
Here below is an example of a registry hack, for more ideas see the side menu.
Instructions for Setting DontDisplayLastUsername
- Launch Regedit. (See more details on starting regedit)
- Navigate to:
HKLM\Software\Microsoft\Windows\CurrentVersion\ Policies\System\DontDisplayLastUserName
Set: DontDisplayLastUsername = 1 - Tip: In regedit, click on the Edit menu, ‘Find’: DontDisplayLastUsername
- To see the effect, try a Logoff / Logon to the Vista Machine
- Double check the logic of ‘don’t display the last username’ (1 = Yes: don’t. Whereas, 0 = No: Do)
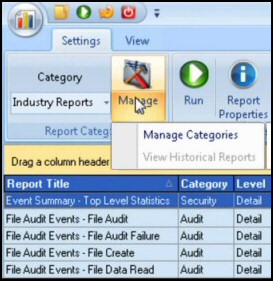
Guy Recommends: SolarWinds’ Log & Event Management Tool
LEM will alert you to problems such as when a key application on a particular server is unavailable. It can also detect when services have stopped, or if there is a network latency problem. Perhaps this log and event management tool’s most interesting ability is to take corrective action, for example by restarting services, or isolating the source of a maleware attack.
Yet perhaps the killer reason why people use LEM is for its compliance capability, with a little help from you, it will ensure that your organization complies with industry standards such as CISP or FERPA. LEM is a really smart application that can make correlations between data in different logs, then use its built-in logic to take corrective action, to restart services, or thwart potential security breaches – give LEM a whirl.
Download your FREE trial of SolarWinds Log & Event Management tool.
Faster kill for applications not responding
HKey\Users\??\ControlPanel\Desktop\WaitToKillAppTimeout default is 20000 milli seconds so try about 5000
As you may guess from the name this sets the timeout on processes that are hanging. Technically this an interesting hack as you have to set it two or thee times in the registry – keep pressing F3 (Find next). The reason is that this setting is found on the Current user, Default user and maybe another user where you see a SID value.
Learning Points
- Particularly with the HKEY_USER registry settings, you have to make the changes three times; remember F3 to ‘Find Next’.
- Time values are in milli seconds e.g 1000 = 1 second
If you like this page then please share it with your friends
More Windows 7 Registry Tweaks
- Gpedit – Local Group Policy Editor
- Editing the Windows 7 Registry with PowerShell
- PaintDesktopVersion (Build Number)
- Change the Name of a Windows 7 Computer
with LocalizedString - Hide User From Welcome Screen
- RegisteredOwner – Windows 7 Registry Hack
- NoDriveTypeAutoRun
- Delete Roaming Profile Cache
- Windows 7 .Reg Files Examples
- Performance Monitoring