The SCP system is a secure way to copy files over a network. In fact, the letters “SCP” stand for “secure copy.” Secure copy gets its name from the Unix command to copy files, which is “cp”. SCP is not a patented command, it is just a concept, like a protocol, that creates a secure way to copy files within the directory system of one computer, or to move files across a network.
Isolating a good SCP server is a difficult task. This is because SCP is usually implemented just as a command and the issue of whether the source or destination of the transfer to the server is conceptually difficult. The SCP command takes two parameters. The first command names the file to copy from and the second is the file name to copy to. You can make either of those filenames a remote file. So, you can copy files from your computer to another computer or from that other computer to your computer. The computer you are on doesn’t even need to be either the source or the destination of the transfer because you can make both remote computers.
The search for a good SCP server is made a little more complicated by the Secure Shell, which is also known as “SSH”. The security for SCP is provided by SSH, so a standard copy performed within an SSH session counts as SCP. If you find it tough to locate an SCP server that you like, it is perfectly valid to consider an SSH server. Servers enable file transfers, so any server that is protected by SSH will have a copy function, creating SCP. So, we cast our net wide when identifying the best SCP server.
Here is our list of the best SCP servers for you to consider:
- SolarWinds SFTP/SCP Server (FREE TOOL)
- Dropbear SSH
- Bitvise
- Free SSH
- OpenSSH
- OpenSSH for Windows
- ZimmerSCP
- WinSCP
- Ish
- HSCP
Now you can read about each of these options in detail.
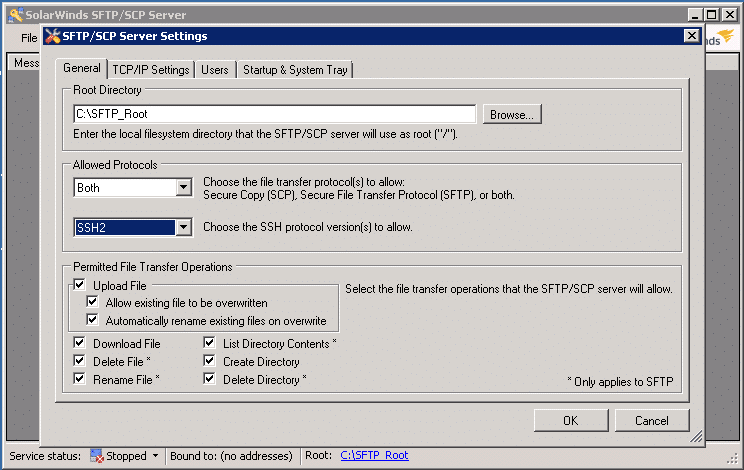
1. SolarWinds SFTP/SCP Server (FREE TOOL)
The SolarWinds SFTP and SCP server is a free utility that installs on Windows. The server has two modes of operation: SFTP and SCP. The main purpose of this tool is to transfer configuration files, firmware updates, and OS images to network equipment and copy settings from network devices to a backup server. Although SolarWinds designed this tool for administration files, it could be used for a wide range of file transfers because it can handle files up to four gigabytes in size.
Each user that accesses the server needs to have an account because SSH requires user authentication. The SolarWinds SCP implementation implements a user identification system that is separate from the native Windows accounts. That means that you need two levels of accounts, one for the operating system and one for the server. That means extra administration, but a benefit of this configuration is that if compromised, accounts in the server do not give data thieves access to the any of the computers on the network.
The SolarWinds option is at the top of our list because it is one of the very few secure servers that actually implements SCP. The others on this list are SSH servers with copy functions. You can download the SolarWinds SFTP and SCP server as a free tool here.
2. Dropbear SSH

Dropbear SSH offers you a way to implement SCP on Linux computers. It will also run on Unix and Mac OS. This utility is intended for use when distributing firmware updates to Linux-based equipment. The server has an interesting feature that allows you to route transfers through specific equipment. This connects with SSH to create a series of tunnels that each has a specified destination – forcing the route to pass through the nominated equipment.
This is an enthusiast-written tool, so there isn’t a big corporation behind it to offer support. You can download the code, so if you have programming skills, you could adapt it, or integrate it into a front-end utility of your own design.
3. Bitvise SSH Server
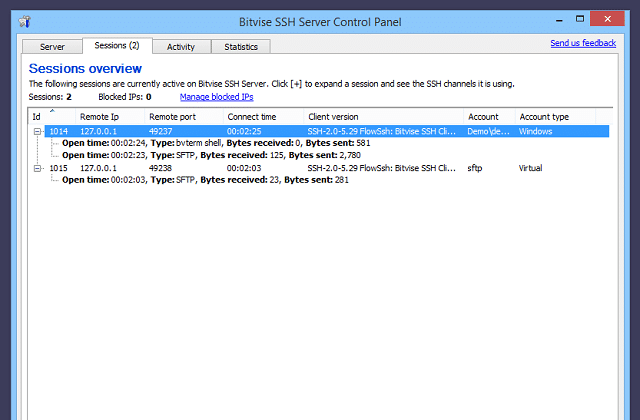
Bitvise is a Windows utility with options for user account types. The interface can operate with native Windows user accounts and it also gives you the option to create virtual user accounts that are only valid within the SSH server system.
Windows has a few security vulnerabilities that make granting SSH access to a computer a little risky. With SSH access, a malicious user could access PowerShell and run a wide range of services that could corrupt the system. Bitvise SSH Server has an administrator account that regular users can’t access. The administrator can restrict the functions of the server so that it only implements SCP. As SCP only includes file transfer capabilities and does not include any command language, this setting greatly reduces the risks that could arise from allowing people to send files with an SSH server.
4. Free SSHd
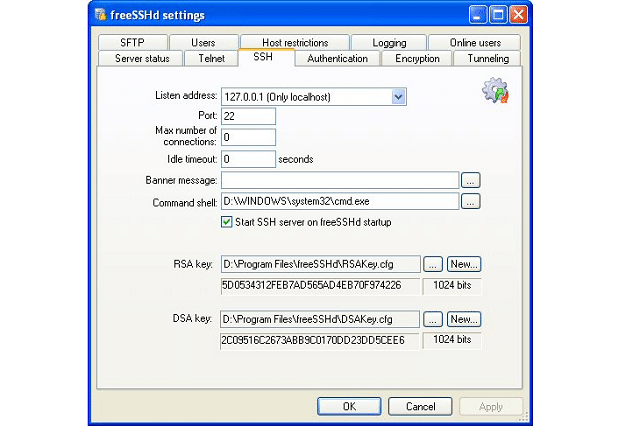
FreeSSHd runs on Windows. It doesn’t actually implement the SCP protocol but it does enable you to use SFTP. The file transfer utilities of SFTP are very similar to the function of SCP. The system runs on Windows NT from version 4 and up. This server integrates user accounts and, being wider than just an SCP server, gives remote access to a target computer. It is possible to execute commands remotely through this tool.
5. OpenSSH

OpenSHH is a free and open source SSH implementation. This system is one of the original SSH implementations that many of the others on this list are based on. OpenSSH runs on Linux and it is also able to operate on Unix, and Mac OS.
The software is developed by volunteers and you can download and change it yourself, or just install it. The file handling functions of the system are based on SCP and there are also SFTP capabilities in the system. As you are allowed to change the source code, it would be possible to disable the remote access functions of OpenSSH and pair it down just to its SCP capabilities.
User authentication requires an account on the target computer. So, if you do customize the program for speed, don’t hard-code the credentials. Another way to limit security risks is to limit file system access to the user’s home directory which should not have root privileges.
6. OpenSSH for Windows

You can also use OpenSSH on Windows. The OpenSSH for Windows tool is a blend of the OpenSSH program and a system called Cygwin. The Cygwin tool enables programs written for Unix and Unix-like systems, such as Linux and Mac OS to run on Windows. You could install Cygwin and then run OpenSSH on top of that. However, the OpenSSH for Windows package does that combo for you.
7. ZimmerSCP
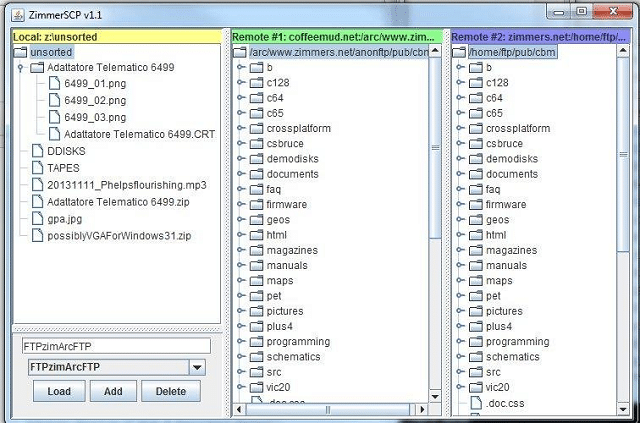
ZimmerSCP installs on Windows. It has a nice GUI interface that anyone can use without having any technical knowledge. This is a full SCP implementation with encryption and user authentication procedures.
The interface shows a file directory of the local computer plus the directories of the remote computers that it connects to. An interesting feature of ZimmerSCP is that it can connect to two remote computers simultaneously. So, you can look at three directories and copy files between them. This means that you can exchange files between two remote computers. This is a great tool for network managers who want to work remotely.
8. WinSCP

The most popular SCP implementation for Windows is WinSCP, which has now been downloaded more that 113 million times. The tool also includes an SFTP implementation.
WinSCP has a very easy-to-use GUI interface, so if you are not very interested in command line utilities and you want a point-and-click environment, this will probably be your best choice. If you have programming capabilities, you will be able to create controlling programs using the tool’s native scripting language.
The utility can be used for configuration management and it has a combination of functions — text editor, scripting language, and file handling routines — that would enable you to put together a log management tool. WinSCP is a flexible tool that could support a lot of network administration functions. However, be careful about who you give access to because the interface also includes remote execution capabilities. Fortunately, the tool will only give remote access to those who already have user accounts on the target computer.
9. Lsh

Lsh is a volunteer-written SSH implementation that operates at the command line on Unix and Linux. Installing this utility is pretty complicated because it requires you to set up the encryption system manually as a separate service. Lsh is a programmer-friendly SSH implementation that will enable you to set up your own SCP server. However, if you don’t have any programming skills or any interest in customizing your own SCP server, you would be better off opting for one of the more complete packages in this list.
10. HSCP
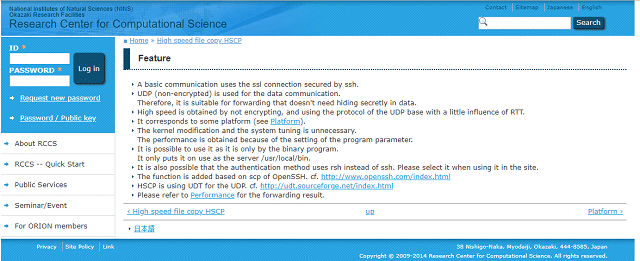
HSCP is the High Speed Copy utility. It squeezes extra speed out of SCP by substituting UDP as the transport protocol instead of the usual TCP methodology. This is a little strange because the encryption methods of SCP require TCP for session establishment. HSCP employs the user authentication procedures of SSH, but they can be turned off.
It seems a little unlikely to take a secure version of a file copy function and then strip off the security. Essentially, this is an alternative to FTP, which is SFTP without the SSH security. Although this utility is fast at transferring files, it has absolutely no security measures, so it should only be used on private networks and not on the internet.
Alternatives to SCP
SCP is not your only option when looking for a file transfer system. The classic file transfer system is FTP, which is one of the oldest networking protocols still in operation. FTP, which is the File Transfer Protocol doesn’t include any security and so it isn’t really a rival to SCP.
FTP variants
There are several adaptations of FTP that integrate encryption and provide security. The main secure FTP systems are SFTP, FTPS and FTP over SSH. SFTP has a lot in common with SCP because its security is provided by SSH – some people call it SSH FTP and others call it Secure FTP. So SFTP is a blend of the SSH and FTP standards. FTP over SSH is the practice of creating an SSH connection and then starting an FTP session within that.
FTP over SSH is not a very good plan. The two systems that create the technique are not really compatible. This is because FTP actually requires two connections running simultaneously. However, SSH creates a single session that in usual implementations takes over the command line of the computer. So, it is difficult to set up a second session to carry the FTP control channel. SFTP doesn’t encounter the same problems as FTP over SSH because the creation of the SSH session is invoked from within the FTP environment, enabling two secure channels to be set up in the background while presenting one session to the user.
SFTP and SCP have the most in common. This is because both act as a blend of SSH with file transferring systems. FTP, and therefore SFTP, creates a session with its own command language that is distinct from the command language of the host operating system. This environment includes commands to query the remote directory, create, delete, or rename directories, and delete files on the remote computer. SCP is a single command that just copies a file from one location to another.
FTPS is another FTP variant that might help you to securely move files from one computer to another. This is FTP Secure, or FTP-SSL. This uses the SSL system of security which was invented to protect internet transactions. This is the surety addition that turns HTTP into HTTPS. SSL stands for the Secure Socket Layer. The protocol has been replaced by Transport Layer Security. So, really, when systems refer to SSL, they really mean TLS. However, the term “SSL” has become so embedded in the networking lexicon that people still tend to apply it to TLS. So, the difference between FTPS and SFTP is that SFTP uses SSH for its security and FTPS uses SSL.
TFTP is another file-handling protocol that you will come across regularly in your network administration career. This is the Trivial File Transfer Protocol, which doesn’t represent a serious alternative to SCP because it does not include any security. TFP is very lightweight and so it is commonly used to transfer small configuration files around a private network. However, its lack of security means that it is almost never used for transfers across the internet.
SSH or SSL
SCP and SFTP both get their security procedures from SSH, whereas FTPS uses SSL, which is the same as saying that FTPS uses TLS. What is the difference between SSH and SSL? Should you use TLS instead of SSH? There are very few fundamental differences between these two security systems.
SSH is usually used for remote execution of commands. The key difference between SSH and SSL/TLS is that SSH requires user authentication. Essentially, an SSH session allows the user access to the command line of the remote computer, so while in an SSH session, the user accesses the remote computer as if he was sitting directly at a terminal in the office where that server is located. You may have heard of Telnet, well SSH is the secure replacement for that application.
SSL is known for its transfer security that is based around certificates. The system uses asymmetrical keys where the cipher key needed to decrypt a message is different to the key used to encrypt it. The decryption key can be made public because the encryption key cannot be derived from it and stays private. Nowadays, SSL is provided by the Transport Layer Security protocol because security weaknesses were discovered in SSL. A challenge message sent by one computer to the other provides authentication procedures based on the public key contained on the security certificate. SSL/TLS uses computer-to-computer authentication. It has no mechanism for user authentication, like SSH. SSL is usually used for file transfers to or from a specific location on a server.
Although there are a number of security options in the SSH definition, most implementations use TLS to provide encryption. So the security protection in transit for SSH and SSL connections is exactly the same. Both SSH and SSL are equally secure. The only difference is that SSH allows remote access to users.
SCP or SFTP
As there isn’t much difference between SSH and SSL, opting for SSH really isn’t an important decision. However, there remains one more question to answer. What is the difference between SCP and SFTP?
Exactly like FTP, SFTP presents the user with an environment with a list of commands. SCP is just a copy command: copy from this file path and file name to that file path and file name. There is no command language with SCP, just a command structure. Both SCP and SFTP require a username and password for access. However, with SCP, those details are parameters to the command but SFTP demands those credentials when opening a session. SFTP creates a session through which many transactions can occur and some remote commands can be executed but SCP is a connectionless one-time execution of a task and does not include any remote execution functions. The lack of command access makes SCP a safer option because it can’t be used to get remote access to a target’s operating system.
Choosing an SCP server
When you are looking for an implementation of the Secure Copy protocol, you can afford to be a little flexible. As far as file transfers are concerned, SCP and SFTP are exactly the same. SFTP has a few extra frills because it allows you to issue some file managing commands on the remote computer. So, if you are looking for an SCP server, you have more or less achieved your goal if you decide to install an SFTP server.
Similarly, most SSH software implementations that include a graphical interface usually offer you a few extra utilities and file copying is often one of those. So, if you settle on an SSH app that includes a file copying function, you have managed to find yourself an SCP client that can also act as a server.
All of the utilities listed in this guide are free to use, so you don’t have to worry about cost and can test a few of them. Check out an SCP server, a TFTP server, and an SSH server, and see which of those you prefer.