Windows Server 2008 – UAC (User Account Control)
The mission of this page is to explain the purpose of Windows Server 2008’s ‘Continue’ pop-up dialog box. I will also show you how to disable this UAC (User Account Control) box.
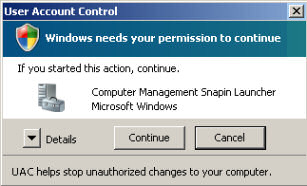
Whenever you need to configure a Windows Server 2008 setting, even if you are logged on as the administrator – you need elevated privileges. This is by design, and part of the fierce security initiative in Windows Server 2008. Before you can complete any administrative task, the User Account Control manager pops-up with a ‘Continue’ message.
Topics for User Account Control in Windows Windows Server 2008
- How to Disable UAC (User Account Control)
- Windows 8 Disable UAC
- Registry Hack to control User Account Control
- Example of User Account Control (UAC)
- Evolution of Windows Server 2008 User Account Control
- CMD Prompt – Run as Administrator
- Disable UAC Windows Server 2012
♦
How to Disable User Account Control (UAC)
If you feel a little guilty when you disable the UAC – join the club. Many techies:
a) Get rid of the nagging ‘Continue’ pop-up message box.
b) Feel shamefaced at turning off this Windows Server 2008 security feature.
c) Sometime later, they realize that the UAC is necessary for security, and turn it back on.
Microsoft’s introduction of UAC reminds me of the governments introduction of seat belts in the 1970s. Both were unpopular at first, but eventually, the majority see the advantages of safety over ease-of-use.
As someone who hated the UAC at first, I can say that now I have turned it back on, firstly, it’s not THAT irritating, secondly it sends a subliminal message ‘Guy work securely’. Thirdly, as an unexpected bonus the delay, or pause, that UAC introduces makes me think more about the action I am about take. – No bad thing!
- Local Policy – Elevate without prompting
- Run all administrators in Admin Approval Mode
- Registry Hack – ConsentPromptBehaviorAdmin
- How to Activate the Hidden Windows Server 2008 Administrator Account
Local Policy – Elevate without prompting
For computers that have joined a domain, ‘Elevate without prompting’ is the best Local Policy method for disabling the UAC pop-up. For Windows Server 2008 Home Editions, or any Windows Server 2008s not joined to the a domain see below.
Stage 1) Preliminary task:
Our first task is simply to launch the Local Security Policy snap-in. You have the choice of two methods:
Method A) Begin by clicking on Windows Server 2008’s Start button, then type secpol.msc in the Start Search dialog box. Note: you must include the .msc extension. See more on Secpol
Method B) The goal is to display Windows Server 2008’s Administrative Tools. Firstly, right-click the Taskbar, select Properties. Next navigate this path: Start Menu, Customize, Advanced; scroll to the bottom and find System Administration Tools, place the radio button next to ‘Display on the All Programs menu’.
Stage 2) Configure the Security Options
- Open the Local Security Policy. (See Method A or B above)
- Expand the Local Polices folder, see the screenshot opposite.
- Drill down to Security Options folder.
- Scroll down, and locate the family of settings beginning with ‘User Account Control’.
- Focus on: User Account Control: Behaviour of the elevation prompt for administrator. Double click and set to: Elevate without prompting. Check the screenshot below.
- Restart you Windows Server 2008 computer.
- When the computer restarts, try to configure a tasks that needs UAC. For example, change the computer’s display name. Press the Windows Key + Pause / Break. Select the ‘Change Settings’ shield.
- UAC should now be turned off, thus you should not see the ‘Continue’ box.

Run all administrators in Admin Approval Mode
There is an alternative, if inferior, method of turning off UAC, that is by disabling the Local Policy, Security Option: ‘Run all administrators in Admin Approval Mode’. Double click and set to ‘Disabled’. Unlike the Elevate without prompting technique, this method turns off UAC and compromises security. My advice is leave this setting as Enabled, and focus on the above setting:
User Account Control: Behaviour elevation prompt for administrator.
Guy Recommends: Permissions Analyzer – Free Active Directory Tool
I like thePermissions Monitor because it enables me to see quickly WHO has permissions to do WHAT. When you launch this tool it analyzes a users effective NTFS permissions for a specific file or folder, takes into account network share access, then displays the results in a nifty desktop dashboard!
Think of all the frustration that this free utility saves when you are troubleshooting authorization problems for users access to a resource. Give this permissions monitor a try – it’s free!
Download Permissions Analyser – Free Active Directory Tool
Other User Account Control (UAC) Settings
As you can see in the above screenshot, there are more server policies for the UAC. However, they are less important and control specialist situations, for example, installing applications.
User Account Control: Detect application installations and prompt for elevation. For home users, the default is Enabled, meaning home users get a UAC dialog box. However, for domain users this UAC is disabled so that installation can proceed silently.
There are similar UAC Policy settings for Users rather than Administrators.
Only elevate UIAccess applications that are installed in secure locations
The idea behind this policy is that Windows Server 2008 will only give UIAccess privileges and user rights to executables that are launched from %ProgramFiles% or %windir%. The permissions are set on these directories to ensure that the executable is not user-modifiable (which would otherwise allow elevation of privilege).
Registry Change to User Account Control
Group Policy settings ultimately work by changing the registry settings. It follows that you could edit the registry directly rather than configure through the Local Policy GUI. When you are learning and if there is a GUI, that is always the best place to start. However, there may be occasions when you need to go to the registry, for example to create a .Reg file. If you would like to examine the key UAC registry settings, then See more about ConsentPromptBehavior here.
One of the underlying computer dilemmas is productivity versus security. If Microsoft make UAC too difficult, then Administrator’s will investigate registry hacks that make their jobs easier, even if easier means a less secure environment. On my test network I move the imaginary productivity -v- security slider to ease of use, whereas for customers, I move the same slider over to more secure settings.
CMD Prompt – Run as Administrator
My problem occurred when I wanted to run the command: ipconfig /release. What I received was this error message:
‘The requested operation requires elevation’.
Fortunately, the solution was easy; as you can see from the screen shot to the right, just right-click the Command Prompt and select Run as administrator from the shortcut menu. As a result I was allowed to run ipconfig /release. There was no irritating: ‘The requested operation requires elevation’.
An Even Better Solution – Tick Advanced Box
When you have found a good move in chess or bridge, always look for a better one. Applying this principle to the CMD prompt:
Right-click the command prompt icon, Properties
Select the Shortcut (tab)
Click on Advanced (button)
Tick: Run as administrator
Overview of UAC
Windows Server 2008s User Account Control (UAC) enables you to wear two ‘hats’. Firstly, when you logon as an administrator, you can run applications such as Outlook, but in the context of an ordinary user. Secondly, whenever you need to put on your Administrator’s hat, UAC prompts you the necessary rights, all you have to do is click ‘Continue’ and receive permission to complete that one task.
An Example of User Account Control (UAC) 
Let us consider this situation, you needed to install a driver, Windows Server 2008 presents you with a dialog box. After reading the UAC menu, you click: ‘Continue’ and thus receive elevated rights for the duration of the task. The key concept is you don’t have to logoff and logon as an administrator. Instead Windows Server 2008 just switches tokens, performs the named task, and then returns you to normal user status.
As an example of UAC in action, let us assume that you wish to check the new System Restore settings. You launch the System Icon, (Windows Key and Pause / Break) then you click on ‘System Protection’ and up pops a Windows Security box – even if you are the Administrator. To gain the elevated rights needed to complete your mission, just click the ‘Continue’ button. See screen shot below.
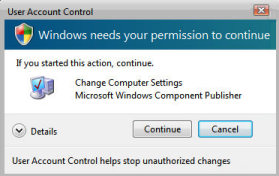
A good habit to cultivate is always to check that the program specified in the central band, is the program you intended; in this case, ‘Change Computer Settings’. Beware that if you are connected to the internet, then sites may have rogue programs that mimic this menu and trick you into installing Spyware.
Microsoft’s New Security Philosophy
UAC is a central plank in Microsoft’s new security fortress. As with so much of Windows Server 2008, Microsoft has redesigned what an ordinary user, or a base-level user can do. Surprisingly, some security settings have been loosened; if a task does not pose a security threat then Windows Server 2008 lets an ordinary user perform that task. For example, in Windows Server 2008 users can now alter the Keyboard, mouse or adjust the Power Settings. As a consequence, this increases the range of activities for a user, and reduce the number of tasks that require Administrative rights, and consequently the need to display the UAC ‘Continue’ dialog box. Naturally if you feel that certain users are getting too much power, then you can clip their wings with Group Policies, which are now increased from 1,500 in XP to 3,000 in Windows Server 2008.
Incidentally, Microsoft use this User Accounts Control system to underpin the Parental Controls on the Home editions of Windows Server 2008.
Guy Recommends: SolarWinds Network Topology Mapper (NTM)
NTM will produce a neat diagram of your network topology. But that’s just the start;Network Topology Mapper can create an inventory of the hardware and software of your machines and network devices. Other neat features include dynamic update for when you add new devices to your network. I also love the ability to export the diagrams to Microsoft Visio.
Finally, Guy bets that if you test drive the Network Topology Mapper then you will find a device on your network that you had forgotten about, or someone else installed without you realizing!
Download your 14 day free trial ofSolarWinds Network Topology Mapper
How User Account Control (UAC) works
If you are familiar with concept of Kerberos in Windows Server 2003, you may already know that once a user logs on successfully, the operating system supplies them with a security token. That token has their privileges and group membership. The whole idea is that the user does not have to keep typing in their password every time they need to open a file or print.
User Account Control extends this idea by supplying what some call a split token and other call two tokens. What ever the semantics, the idea is that to perform jobs such as checking their email or updating their spreadsheets, the Administrator relies on the lesser token, the one with minimal rights. Suppose that same user account now needs to carry out a higher level administrative task, for example, changing a DNS record or amending a DHCP scope option; at this point they need to switch to the other full token, known as Administrator Approval Mode. Thanks to User Account Control, a menu appears with a shield symbol and the clicks ‘Continue’, job done, no need to logoff as a user and the logon as the administrator.
User Account Control – Under the Covers
Imagine a user launching a snap-in from the MMC. The Windows Windows Server 2008 shell calls CreateProcess, which then queries the application to see whether it requires elevated privileges
If the application does not require elevated privilege the process is created through NtCreateProcess – end of story. However, let us assume that the snap-in requires elevated privilege, in this instance CreateProcess, returns an error to ShellExecute.
Next, ShellExecute calls Application Information Service (AIS) and now initiates an elevated launch.
AIS then prompts the user for a password through the Consent User Interface.ShellExecute now tries again, but this time uses the full token to launch the application on the client’s Windows Server 2008 machine.
Evolution of Windows Server 2008 User Account Control
In earlier Beta 1 builds of Windows Windows Server 2008, UAC was called UAP (User Account Protection). More than just a mere change of acronym, this indicates that UAC is part of a larger security area, which Microsoft are rapidly evolving. Following feedback from beta testers, Microsoft fine tuned the balance between high security and ease-of-use for the UAC.
Microsoft’s press releases tell us that User Account Control is a development of least-privilege user access, or LUA. My view is that User Account Control has grown out of the ‘Run as..’ feature of Windows Server 2003 or the ‘Switch User’ feature of XP. I have to say that at least on training courses, RunAs was one of the least liked features of Windows Server 2003.
Even when we ignored ‘Run as…’ on those training courses, we had this feeling of being naughty boys and not taking security seriously. User Account Control makes it easier to develop good habits and work securely. UAC is like opening a locked draw using a plastic card kept in your top pocket, compared with ‘Run as…’, which is like walking over to the filing cabinet and finding the correct key for your draw. In summary, User Account Control automatically gives you the best of both worlds, rely on a basic token for routine tasks and reserve the Administrative token for special security responsibilities.
Surprise, I discovered that certain tasks still need the ‘Run as…’ technique, for instance releasing and renewing an IP address. This is how it works.
Summary of User Account Control (UAC)
User Account Control (UAC) is a central plank in Microsoft’s security platform for Windows Server 2008. This page gives you strategies for controlling this service. One theme that runs through UAC is that Microsoft are still fine-tuning the places where you can configure the settings, there have been significant changes from Beta 1 –> Beta 2 –> RC1 –> Windows Server 2008 Final Release.
If you like this page then please share it with your friends
Microsoft Windows Server 2008 Topics:
• Server 2008 Home • Overview • What’s New? • Migration Advice • Install • SP1 Review
• AD DC • Roles • Features • Editions • Hyper-V • UAC • IPv6 • Group Policy • Free NPM Trial



